Integrate a Splunk Enterprise Security Cloud Device
Configure a Splunk Enterprise Security cloud device to pull IOCs from Digital Risk Protection (Threat Command). You must first add the device to Digital Risk Protection (Threat Command) and then configure the device to pull IOCs from Digital Risk Protection (Threat Command).
Add a Splunk ES cloud device
Add a cloud device to Digital Risk Protection (Threat Command).
Prerequisites
- You have the credentials to access the device.
- You have administrative credentials to access Digital Risk Protection (Threat Command) with a subscription to the Automation and TIP modules.
To add a cloud device to Digital Risk Protection (Threat Command):
- Log in to Digital Risk Protection (Threat Command) at https://dashboard.ti.insight.rapid7.com
- From the main menu, select Automation -> Integrations.
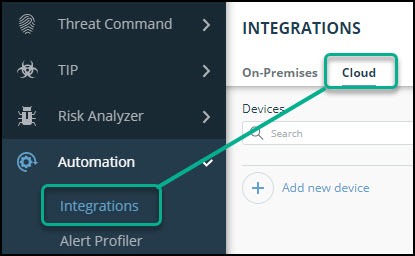
- From the Integrations page, click Cloud.
- Click Add new device.
- In the Add New Cloud Device dialog, type a user-defined name for the device. The name can contain a maximum of 50 letters, spaces, numbers, and underscores.
- Select the Device type.
The default device IOCs limit is displayed. - (Optional) You can change the IOCs limit.
- Click Add.
- To verify that the new device is added, refresh the Automation > Integrations page.
The new device is added to the cloud integrations device list. Next to the device name, there is a red dot, indicating that communication has not yet been established. The dot will change to green when the device is synchronized. If the device cannot synchronize for more than 48 hours, an email warning is sent to the account administrator.
Configure a Splunk ES device to pull IOCs
After a device has been added, you must enable it to pull IOCs from Digital Risk Protection (Threat Command).
Before you begin, ensure:
- You have the device login credentials.
- The device has been added.
- You have administrative credentials to access Digital Risk Protection (Threat Command) with a subscription to the Automation and TIP modules.
- An IOC group for this device exists in Digital Risk Protection (Threat Command).
Creating IOC groups is described in Create an IOC group
Due to device limitations, IOC groups for on-premises devices can consist of only two types of IOCs: domains, URLs, or IP addresses. To support more types, create multiple IOC groups.
You must repeat the following procedure for each IOC group to pull into the device.
To configure a Splunk ES cloud device to pull IOCs:
-
From Digital Risk Protection (Threat Command), open the Splunk Enterprise Security IOC group Device Details screen:
- From the main menu, select Automation > Integrations.
- From the On-Premises (or Cloud ) device list, select the Splunk Enterprise Security (TAXII) device.
- Click the link icon to the far right of the device IOC group.
The Device Details screen displays several fields that need to be copied into the Splunk Enterprise Security console:

-
Log in to the Splunk Enterprise Security management console.
-
Navigate to Enterprise Security > Configure > Data Enrichment > Threat Intelligence Downloads. Current IOC pulls are displayed:

-
Click New.
-
In the Threat Intelligence Download Settings screen, type the following values:
Field Value to type Description Name A user-defined name This name will be displayed in the Threat Intelligence screen. It can be used to search for IOCs. Type taxii Type “taxii” in lowercase letters. Description A user-defined description This description will be displayed in the Threat Intelligence screen. URL The TAXII URL Paste this value from the Digital Risk Protection (Threat Command) Device Details screen. Weight 1 Type the value 1 Interval 43200 Type the value 43200. By default, IOCs are pulled once every 12 hours. Post arguments Post arguments value Copy the post arguments value exactly from the Digital Risk Protection (Threat Command)Device Details screen. This includes the username and password, so those do not need to be added separately. Maximum age NA -
In the Parsing Options section of theThreat Intelligence Download Settings screen, leave the default values.
-
Deploy the changes.
-
If you have more than one IOC group, repeat this procedure for each IOC group.
View pulled IOCs in Splunk ES
Viewing downloaded IOCs in the Threat Intelligence Downloads window can take a long time. You can view the data earlier in the following methods:
Splunk threat artifacts (recommended method)
This viewing method enables seeing all IOCs, including the Digital Risk Protection (Threat Command) enrichment (in TAXII).
- From the main menu, click Security Intelligence > Threat Intelligence > Threat Artifacts.
Splunk search function
This viewing method enables seeing only those IOCs that match the search terms.
- From the main menu, click Search and Reporting.
- In the search field, type:
|`http_intel` |`ip_intel` |`file_intel` | search threat\_key=\*Name\*Where:
-
The single apostrophe marks are all the same (on most keyboards, typed on the key to the left of the 1 numeral key).
-
Name is the exact, case-sensitive name that you configured in the Threat Intelligence Download Settings screen.
You can use any combination of these settings, surrounded and separated by a pipe sign: | Search text | Description | | --- | --- | |
http_intel| Return URLs found in Name | |ip_intel| Return IP addresses and domains found in Name | |file_intel| Return file hashes found in Name |