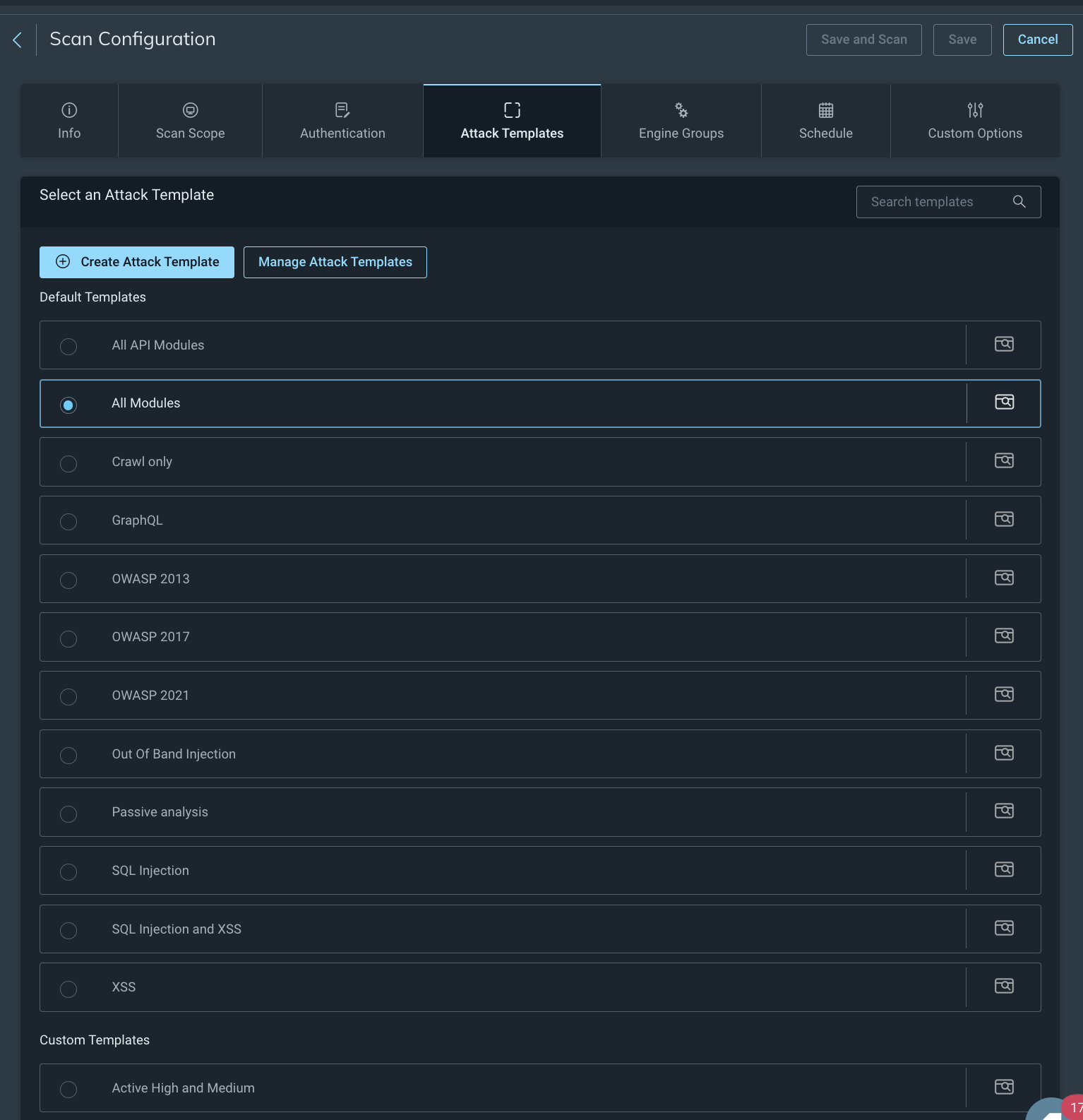
Configure Attack Templates
Attack templates are pre-configured sets of attacks and performance options. Application Security (InsightAppSec) comes with a set of pre-built default attack templates based on common requirements of application security professionals. Application Security (InsightAppSec) also supports custom attack templates to further refine your scan configuration. You can create custom and manage existing attack templates.
Default attack templates
The default attack templates are as follows:
- All modules - Enables all attack modules. This template provides the most comprehensive coverage of vulnerabilities but also requires the most resources.
- We recommend limiting the use of this option to pre-production environments. Using the all modules template can significantly slow or disrupt customer-facing websites.
- The Out of Band Injection for Log4j attack template is disabled by default. For more information, see Detect Log4j.
- All API modules - Enables all API-specific attack modules. Use this template with APIs. It identifies API-specific vulnerabilities, helping to close any gaps in coverage.
- Crawl only - Deselects all attack modules. This template is useful to understand the topology of your app and make an inventory of all the web pages in it.
- You can can either run an unauthenticated crawl scan to discover all the public facing resources of your app, or an authenticated scan to list all the internal as well as external resources.
- Click the Crawl Map button on the Scan page to reveal the topology of the app discovered through the scan.
- GraphQL - Enables all GraphQL-specific attack modules. Use this template with GraphQL schemas or URLs to identify vulnerabilities.
- OWASP LLM Top 10 2025 - Enables attacks related to the most critical LLM application security risks listed in the OWASP LLM TOP 10 2025 report. See the OWASP website for more information: https://genai.owasp.org/llm-top-10/
- OWASP API Top 2023 - Enables attacks related to the most critical API application security risks listed in the OWASP 2023 report. See the OWASP website for more information: https://owasp.org/API-Security/editions/2023/en/0x11-t10/
- OWASP 2021 - Enables attacks related to the most critical web application security risks listed in the OWASP 2021 report. See the OWASP website for more information: https://owasp.org/Top10/
- Passive analysis - Enables only passive analysis modules which find vulnerabilities by analyzing responses from the web application, rather than sending network requests.
- SQL Injection - Includes all SQL Injection related attacks. You can learn more about SQL Injection attacks here: https://www.owasp.org/index.php/SQL_Injection
- XSS - Enables all attacks related to Cross-site Scripting (XSS). You can learn more about XSS attacks here: https://owasp.org/www-community/attacks/xss/
- SQL Injection and XSS - In many real-life scenarios, attackers use a combination of SQL Injection and Cross-site scripting vulnerabilities to gather sensitive data from your application. This template gives you an overall picture of such vulnerabilities in your application.
- Out of Band Injection - Simulates more sophisticated web application attacks that do not use traditional HTTP request-response interactions to determine if you are susceptible to the Log4Shell attack. For more information, see Detect Log4j.
Custom Attack Templates
You can create your own attack templates for scan configs. Customize your attack templates by enabling different attacks, setting attack prioritization, and adjusting the severity, max findings, and attack locations of existing attacks. You can customize the following in your attack template:
- Advanced attacks adds more variations to the attacks being carried out against the target application.
- Browser encoding instructs Application Security (InsightAppSec) that attacks should only be encoded in the default browser encoding. Application Security (InsightAppSec) encodes attack traffic using a variety of character encodings so it can pass through your firewall and attack your application. Many web applications and firewalls test incoming requests against a limited set of character encodings, like UTF-8 and UTF-16.
- No - Encode attack requests using a variety of character sets to bypass firewalls.
- Yes - Only encode attack requests using the character sets specified by the browser.
- False positive regex - Application Security (InsightAppSec) might incorrectly associate certain pages of your applications with 4xx error codes. If you believe that legitimate messages in your web application are being flagged as vulnerabilities, you can add their content to the False Positive Regex field to prevent false positive results.
- Example: The message “This web browser does not support JavaScript or JavaScript in this web browser is not enabled” is only meant to notify the user of missing functionality and is not an indicator of a web application vulnerability. If this is incorrectly flagged as an error message, you can add the string in the False Positive Regex field.
- Attack prioritization controls the order in which attacks are run on target URLs:
- Sequential runs all attacks on the first link, then switches to the next link, and so on. This is easier for troubleshooting, if you want to figure out which module is causing trouble while scanning your web applications.
- Smart uses a Rapid7 proprietary attack prioritization algorithm.
- Randomized randomly selects a link from the attack space to run attacks on. Randomized attacks are harder to detect as automated traffic by firewalls.
- Attack per input controls the number of attacks run by Application Security (InsightAppSec) on every link.
- All - All potential attacks are made.
- Smart - Uses a Rapid7 proprietary attack selection to minimize redundant attacks.
- Time - Attacks that take less time are run before attacks which run longer.
- Active and passive attacks
- Severity sets the default severity applied to findings of the attack template.
- Max Findings sets the maximum number of findings for the attack type.
- Attack Locations sets the locations that Application Security (InsightAppSec) will attack.
Create a custom attack template
You can customize your own attack templates for scan configs.
- Go to the scan config that you want to add a custom attack template to.
- On the Attack Templates tab, click Create Attack Template.
- To set advanced options, click Show Advanced Options and update the options as necessary.
- Click Next: Choose Active Attacks.
- On the Active Attacks tab, enable and disable active attacks.
- To select individual attacks, use the toggle in the Enabled column.
- To bulk enable or disable, click Enable All or Disable All.
- To adjust the attack criteria in the Severity and Max Findings columns.
- Click Next: Choose Passive Attacks.
- On the Passive Attacks tab, customize, enable, or disable passive attacks.
- Click Create Attack Template.
Select an attack template
When you are creating or editing a scan config, on the Attack Templates tab, select any of the default or custom attack templates.
Manage attack templates
You can manage attack templates on the Admin Settings page and on the Attack Templates tab of a scan config.