Microsoft InTune
The Microsoft InTune plugin for Automation (InsightConnect) focuses on allowing users to manage their organization’s devices. This plugin enables users to perform antivirus scans and manage devices in Microsoft InTune - including wiping, syncing, and rebooting those devices. Additionally, users can trigger workflows on new alerts found within Microsoft InTune.
To use the Microsoft InTune plugin, users must set up an application in their Azure Active Directory and then configure the connection in Automation (InsightConnect). For more information on the functionality of the Microsoft InTune plugin, see the Extension Library listing .
Create an application in Azure Active Directory
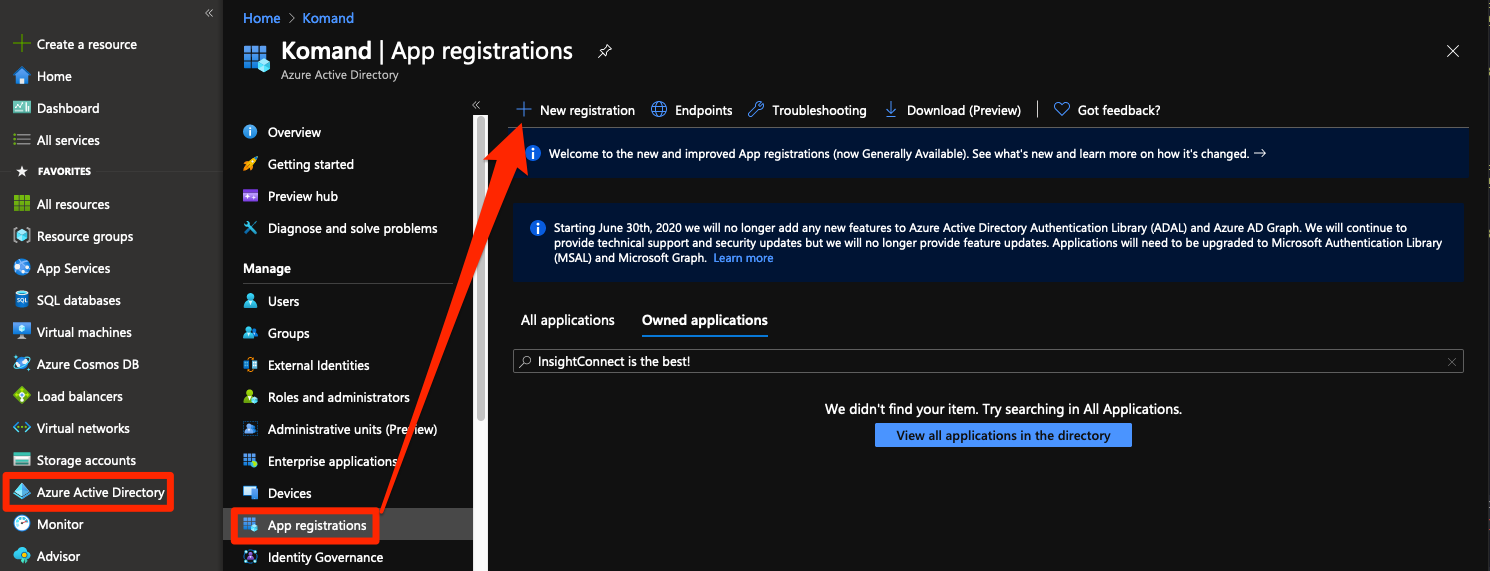
- Log in to Azure Portal with a user that has the Global Administrator role.
- Click Azure Active Directory > App Registrations > New Registration.
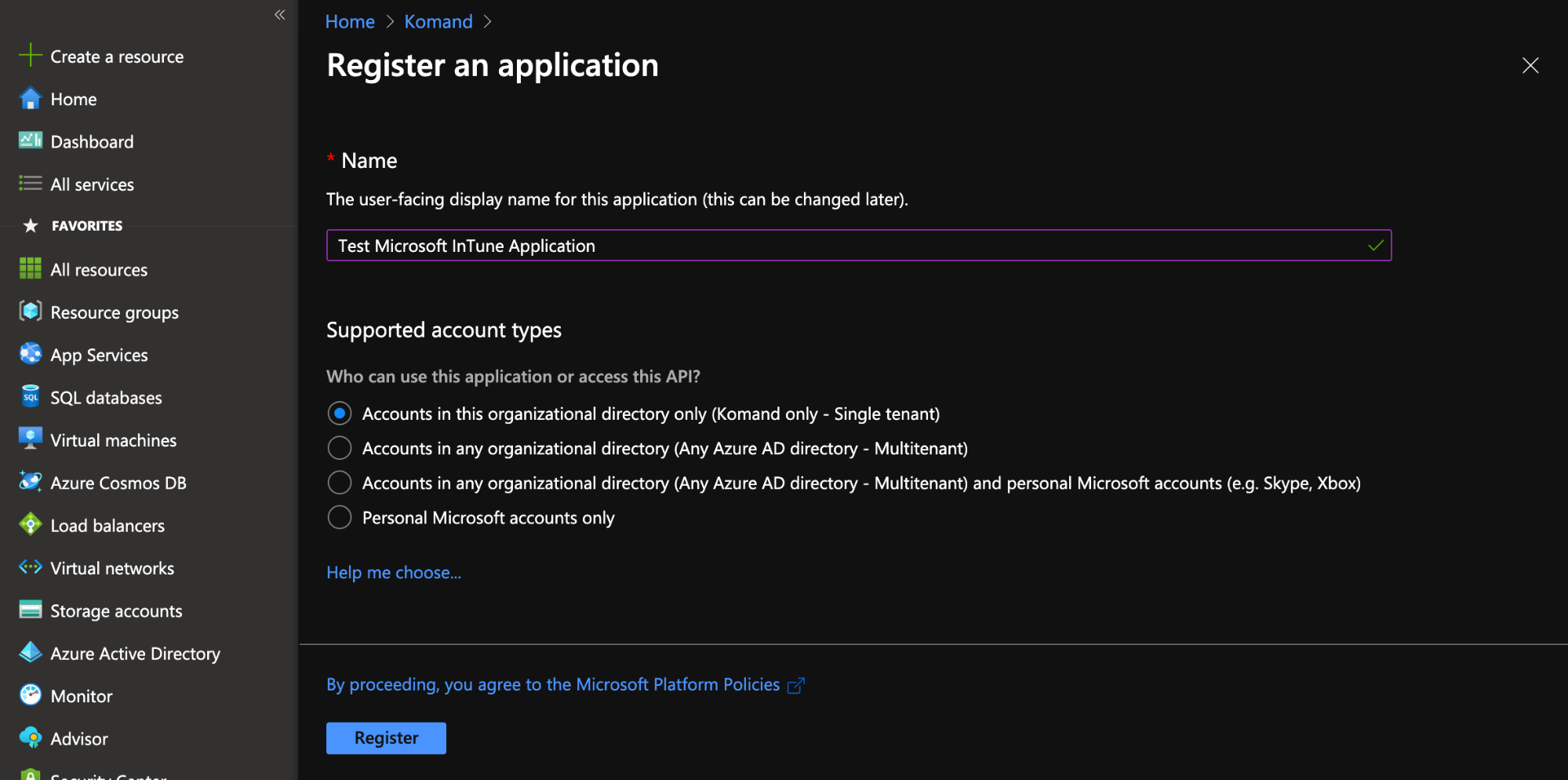
- Name your Application in a way that indicates its purpose and to help you keep track of it, then click Register.
- Now that your application has been created, you must assign correct permissions to enable it to access Microsoft InTune. To do this, click API Permissions > Add a permission.
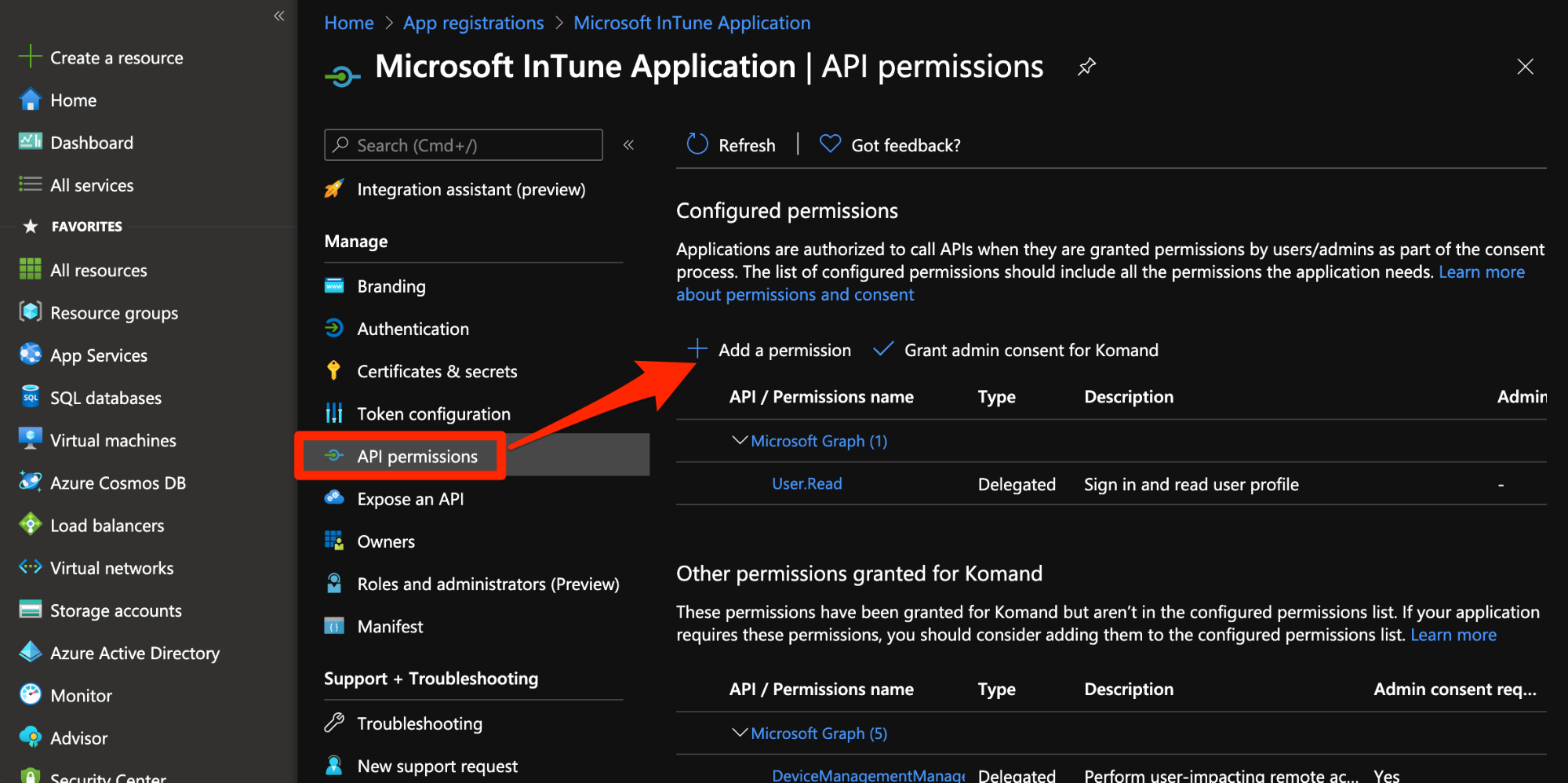
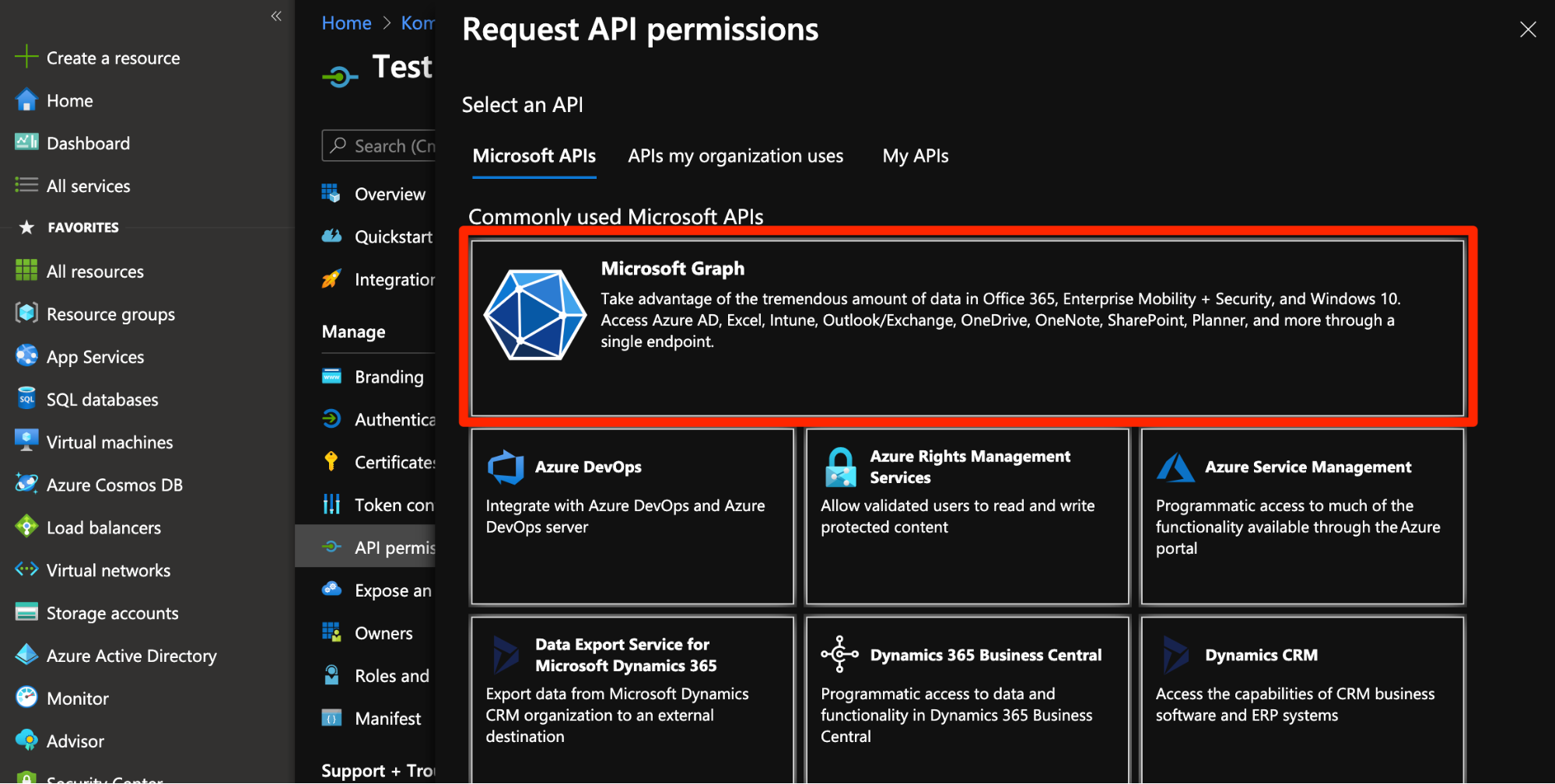
- Select Microsoft Graph.
- Select Application Permissions, and select the appropriate permissions to perform the desired action. The Microsoft InTune plugin requires the following permissions:
DeviceManagementManagedDevices.PrivilegedOperations.AllDeviceManagementManagedDevices.Read.AllDeviceManagementManagedDevices.ReadWrite.All
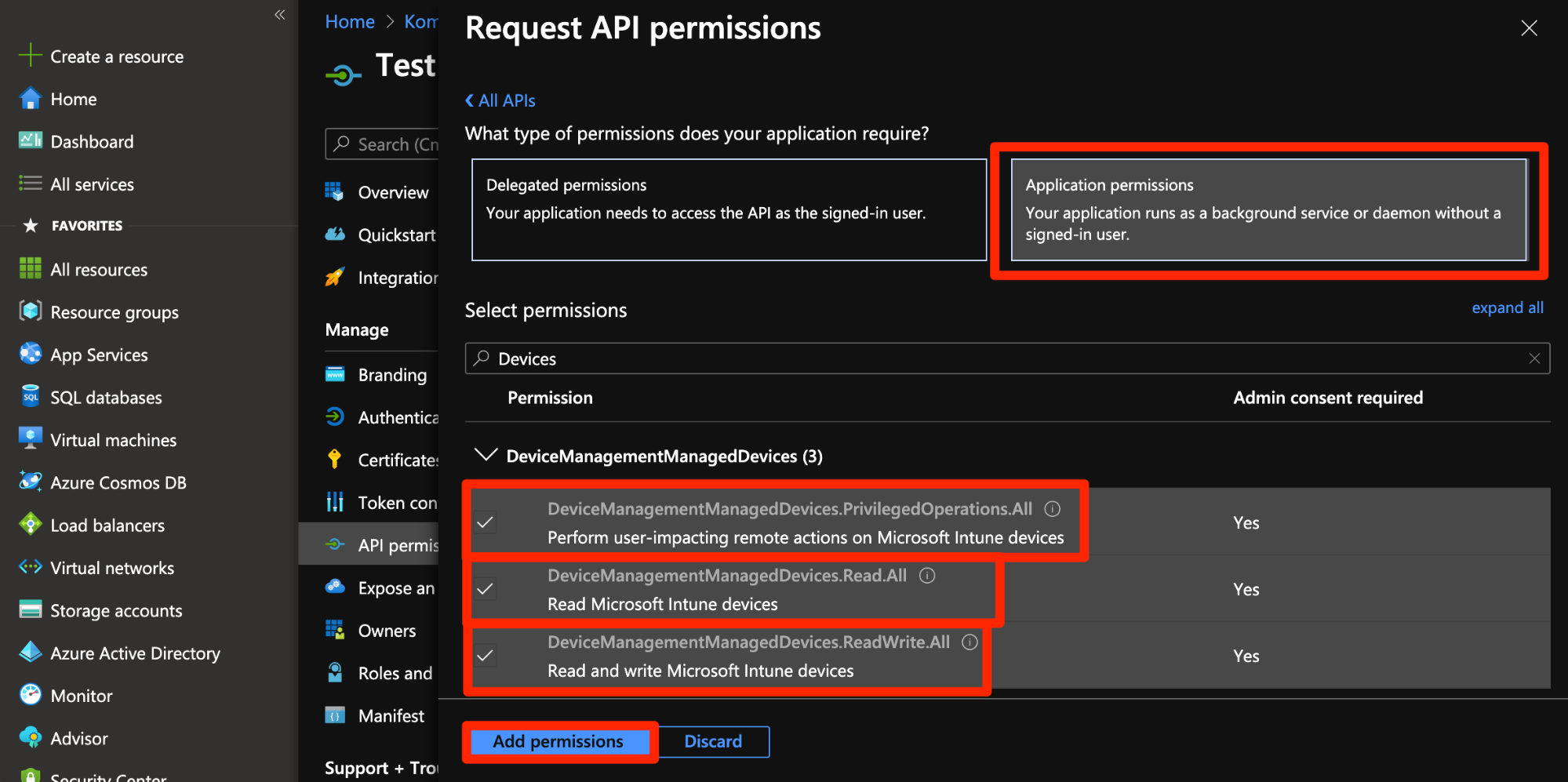
- Once all the desired permissions are selected, click Add permissions.
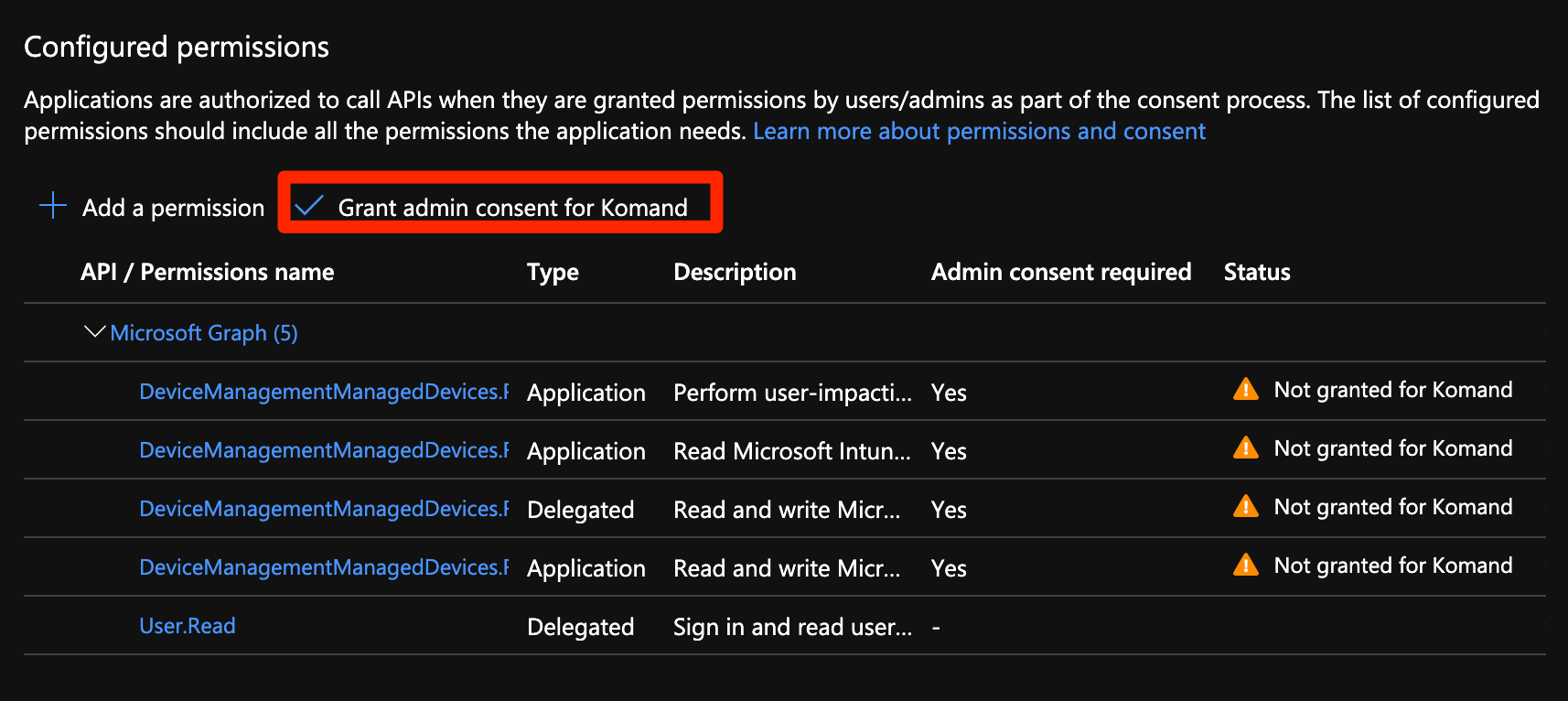
- Grant administrator consent to the permissions selected. Note that every time you add a permission, you must select Grant consent for the new permission to take effect.
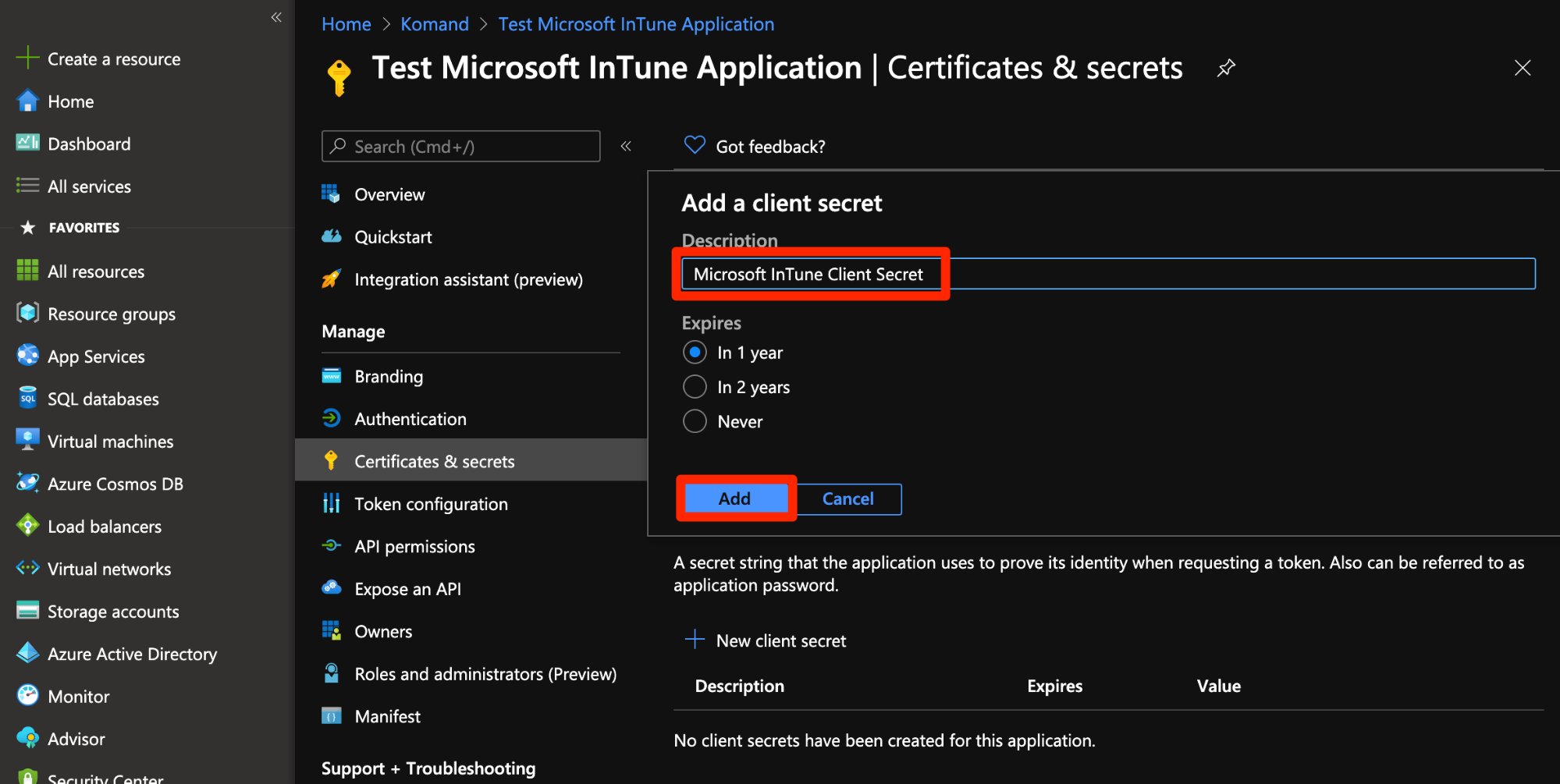
- Now that you’ve configured your application, add an Application Secret to it by clicking Certificates & secrets > New client secret.
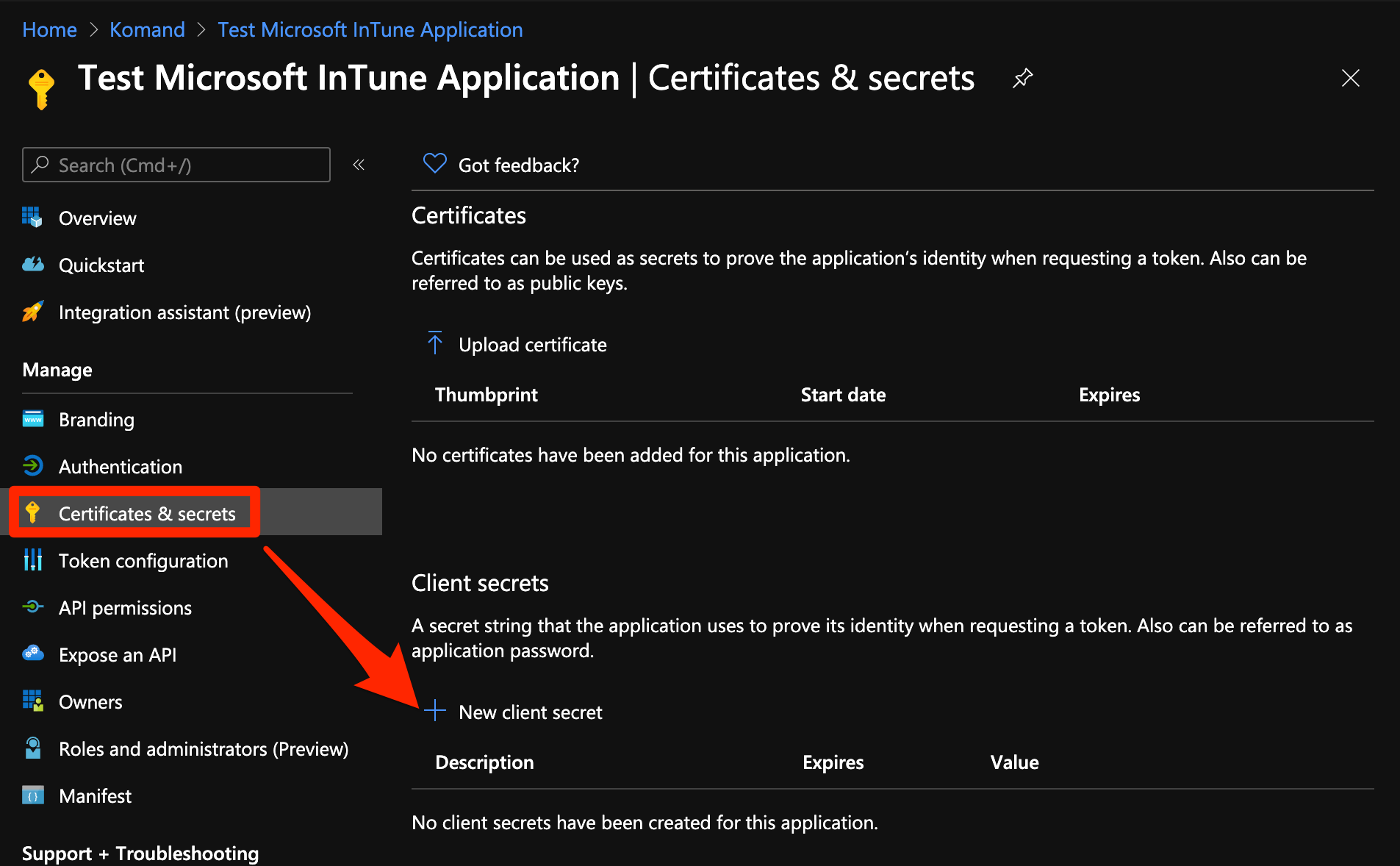
- Enter an application secret description that indicates its purpose and click Add.
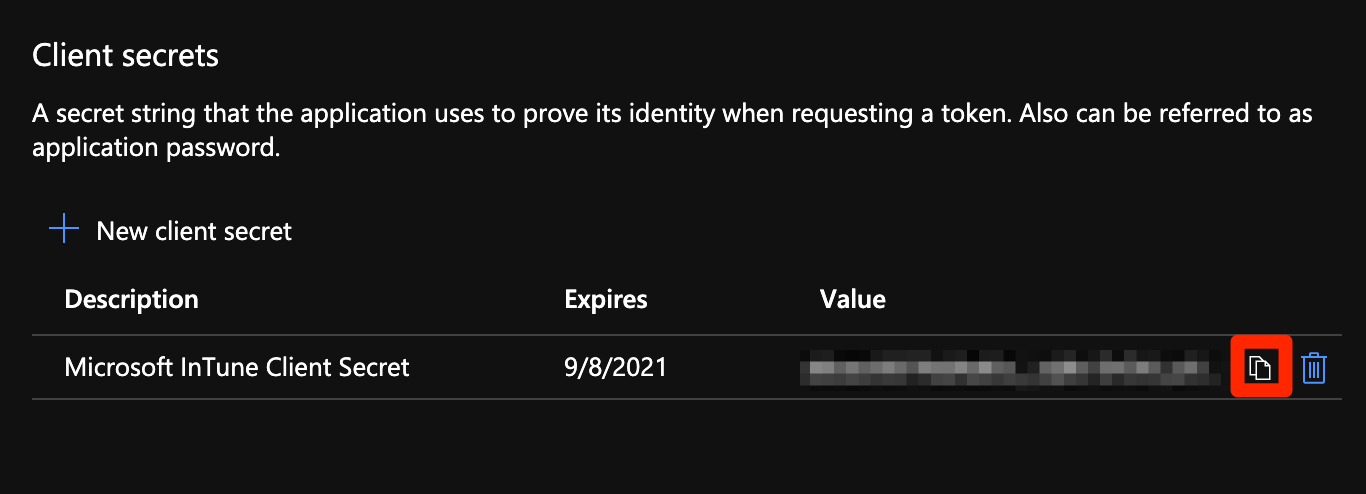
- Copy the generated secret value. You won’t be able to retrieve this value after you leave this screen.
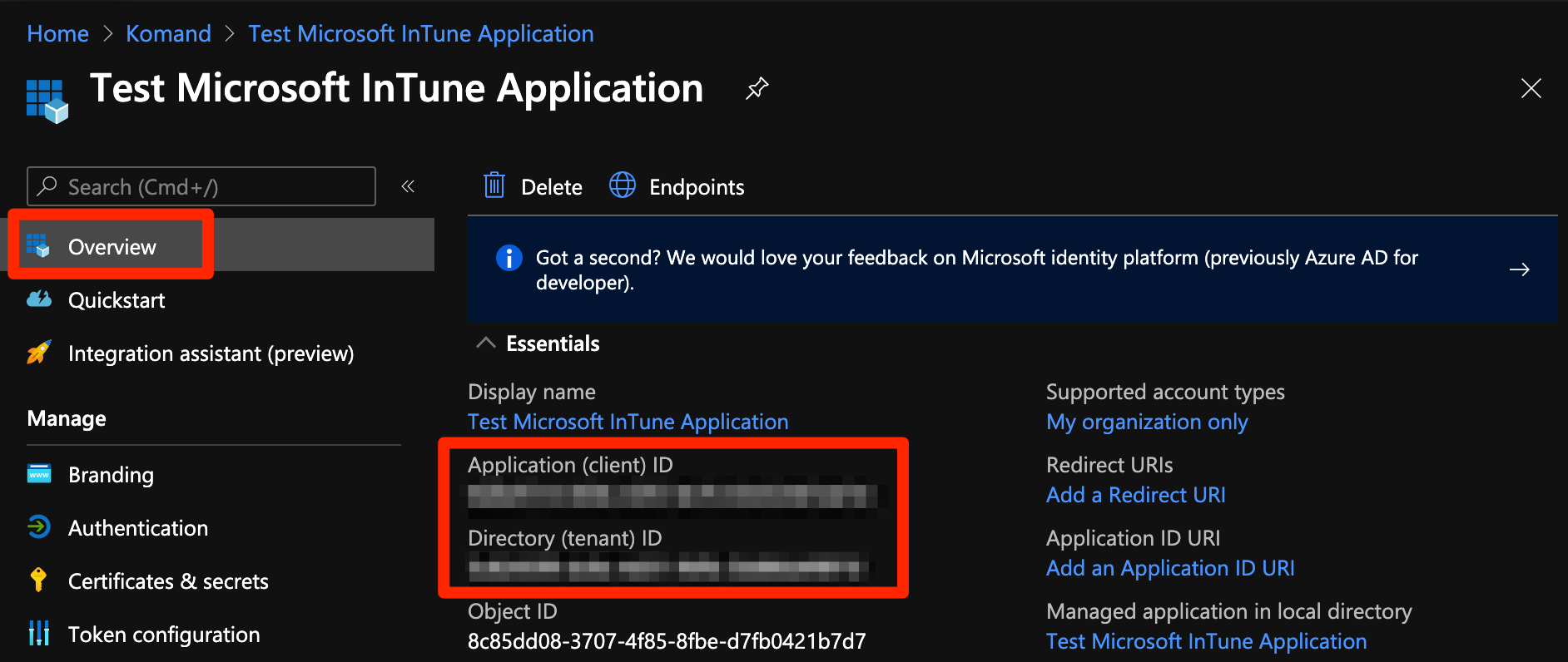
- To get your Application ID and your Directory ID, select Overview and copy the values.
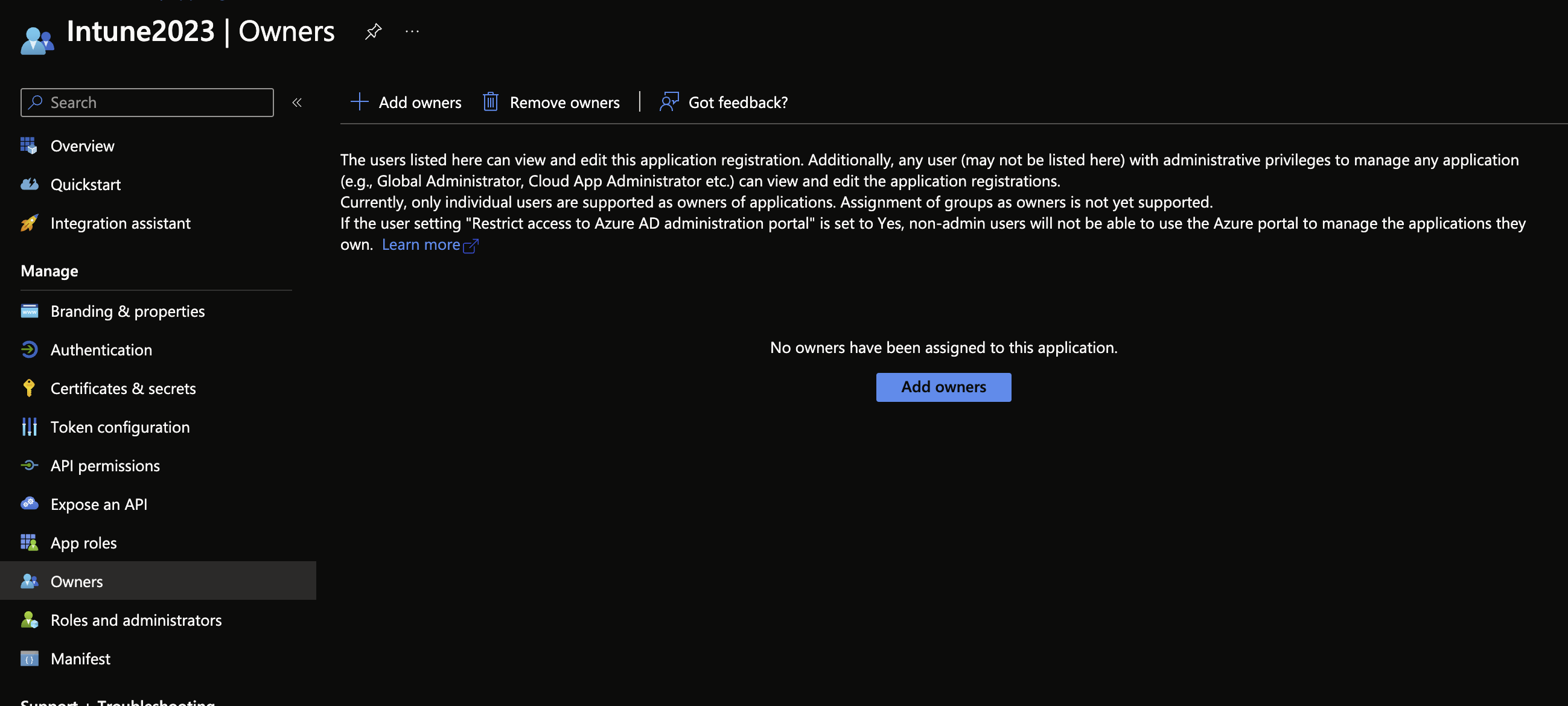
- Select Owners from the left hand pane. Add the user account that will also be used when setting up the connection within Automation (InsightConnect) as an owner of this application.
Configure the Microsoft InTune Connection in Automation (InsightConnect)
Now that you’ve created your application in Azure Active Directory, you can configure the Microsoft InTune connection in Automation (InsightConnect) to use the plugin.
- In Automation (InsightConnect), open the connection configuration for the Microsoft InTune plugin.
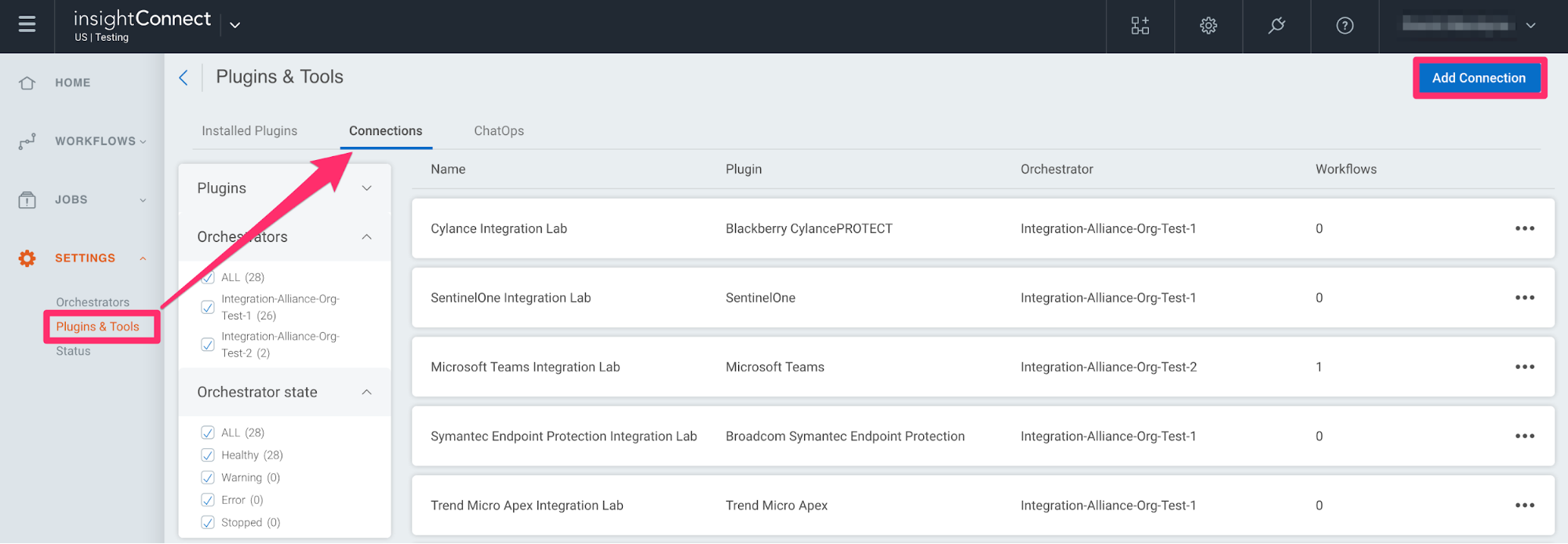
- You can do this when selecting the Microsoft InTune plugin during a workflow building session or by creating the connection independently by choosing Plugins & Tools from the Settings tab on the left menu. On the Plugins & Tools page, select the Connections tab and click Add Connection in the upper-right corner.
- Configure the connection for the Microsoft InTune plugin.
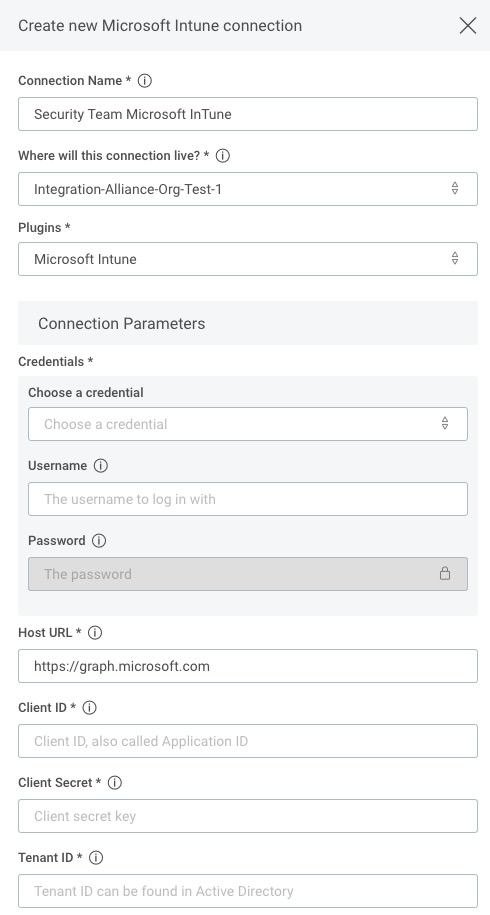
- Give the connection a unique and identifiable name, select where the plugin should run, and choose the Microsoft InTune plugin from the list. If it’s not available, then import the plugin from the Installed Plugins tab.
- Configure your Microsoft InTune credentials.
- In the Credentials field, select existing Azure AD credentials or enter a new username and password. In the host URL field, leave the default value unless you host the graph API. If you host the graph API, enter the URL for your endpoint.
- In the Client Secret field, create a credential and paste in the Microsoft InTune Application Secret that you copied earlier.
- In addition, add the Application ID and Directory ID you copied earlier into the Client ID and Tenant ID fields, respectively.
Success!
The Microsoft InTune plugin is ready to use.
Test your connection
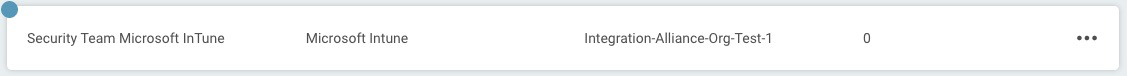
When you save the connection, the connection test will attempt to authenticate to your Azure Active Directory Microsoft InTune application. A blue circle on the Connection tile indicates that the Connection test is in progress.
Successful connection tests
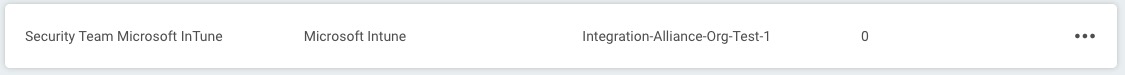
If there is no circle, the connection succeeded and you’re ready to begin orchestrating your processes with Microsoft InTune.
Failed connection tests
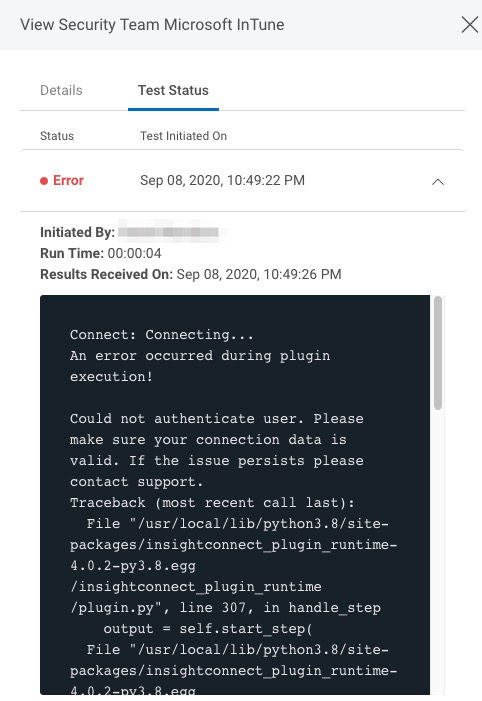
A red circle indicates that the connection test failed. If this occurs, check your connection details (including the username and password, Application Secret, Application ID and Directory ID) before trying again.
The log may contain useful troubleshooting information. First, click View to see a list of your recent connection tests.
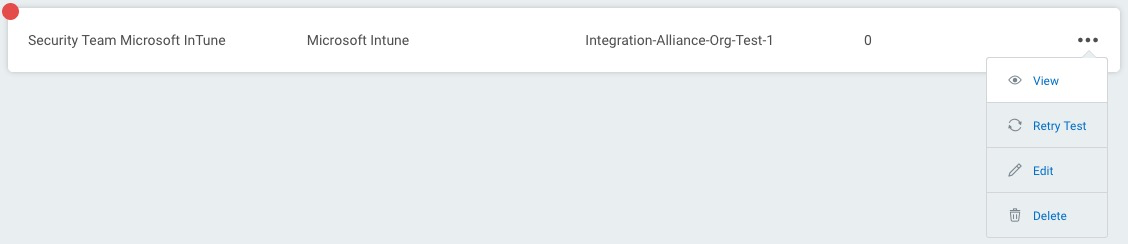
Under the Test Status tab, expand the dropdown for the test that encountered an error to view its log.