Collected Evidence Report
The Collected Evidence Report details all looted information from exploited target hosts. Evidence can be collected from a target host that was successfully exploited and has an open session. Use the collected evidence report after running an exploit to gather the information from the target hosts into a report.
Host vs Target Host
Generated reports refers to “target host” as “host”.
Project Summary
The Project Summary is a synopsis of the project administration data.

- Project Name - The name of the project.
- Started - The date and time the collected evidence phase of exploitation started.
- Completed - The date and time the collected evidence phase of exploitation ended.
- Users - User who worked on the project.
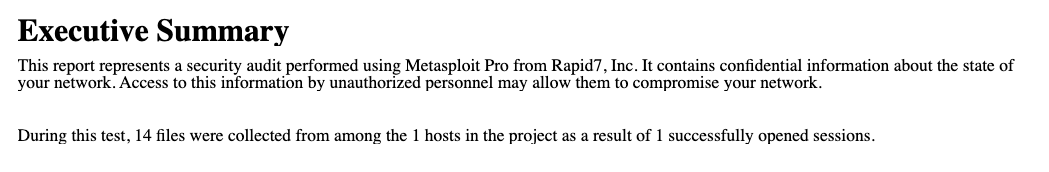
Executive Summary
The Executive Summary gives the number of files collected, number of target hosts in the project, and the number of sessions that were opened.
Collected Evidence Summary
The Collected Evidence Summary shows the number of open sessions and collected files for a target host. If more than one target host opened a session, then it will be listed on a new line.
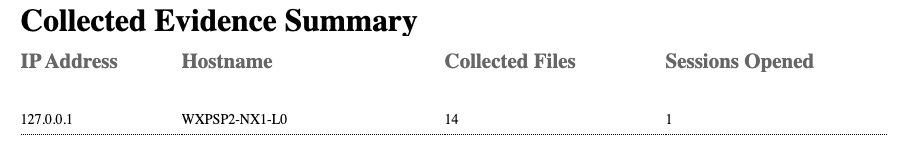
- IP Address - IP address of the target host.
- Hostname - Name of the target host.
- Collected Files - This includes text files and screenshots.
- Sessions Opened - The number of sessions successfully opened.
Collected Evidence List
The Collected Evidence List details looted target host information and the types of content and evidence that were collected.
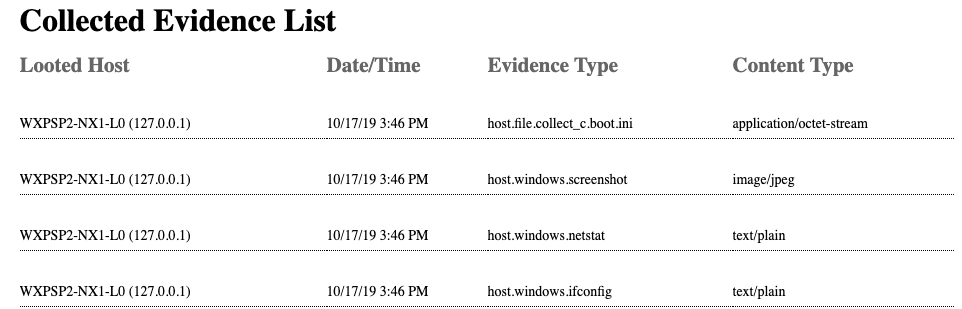
- Looted Host - Name and IP address of the looted target host.
- Date/Time - Date and time the target host was looted.
- Evidence Type - The type of evidence collected.
- Content Type - The type of content collected.
Collected Screenshots
The Collected Screenshots section shows any screenshots collected during an exploit.
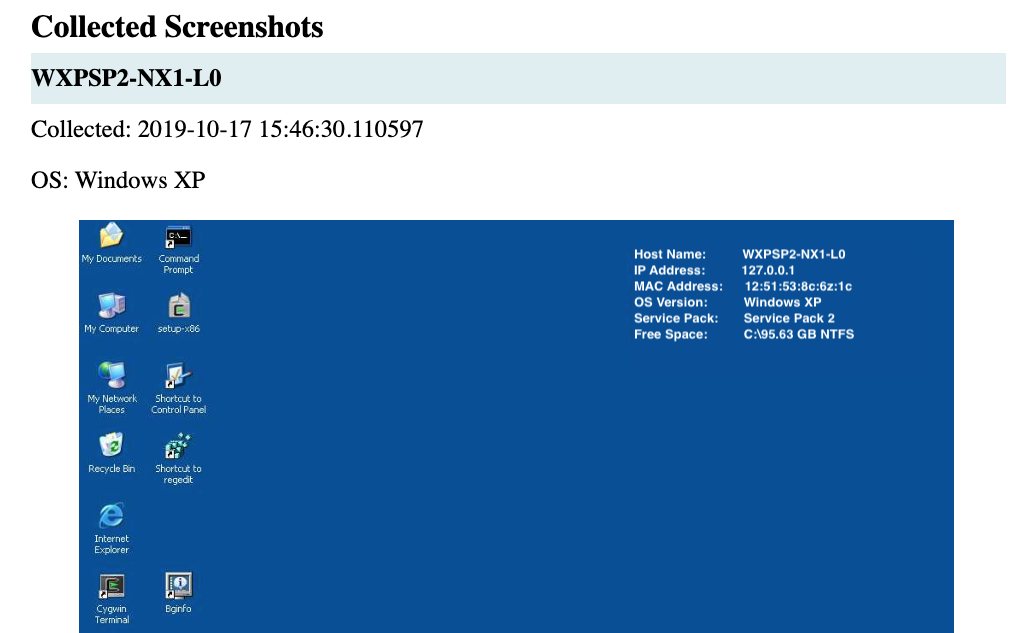
- Hostname - Name of the looted target host.
- Collected - Date and time the screenshot was taken using the format
yyyy-mm-dd hh:mm:ss:fffffffff. - OS -Name of the operating system for the target host.
Host Data Collected
The following data will be collected and added to the screenshot if it is available.
- Host Name - Name of the target host.
- IP Address -IP address of the target host.
- MAC Address - MAC Address of the target host.
- OS Version -Operating system of the target host.
- Service Pack - If applicable, service pack of the target host.
- Free Space - Available hard drive space of the target host.
Collected Text Files
The Collected Text Files section includes a description of the file and its contents.
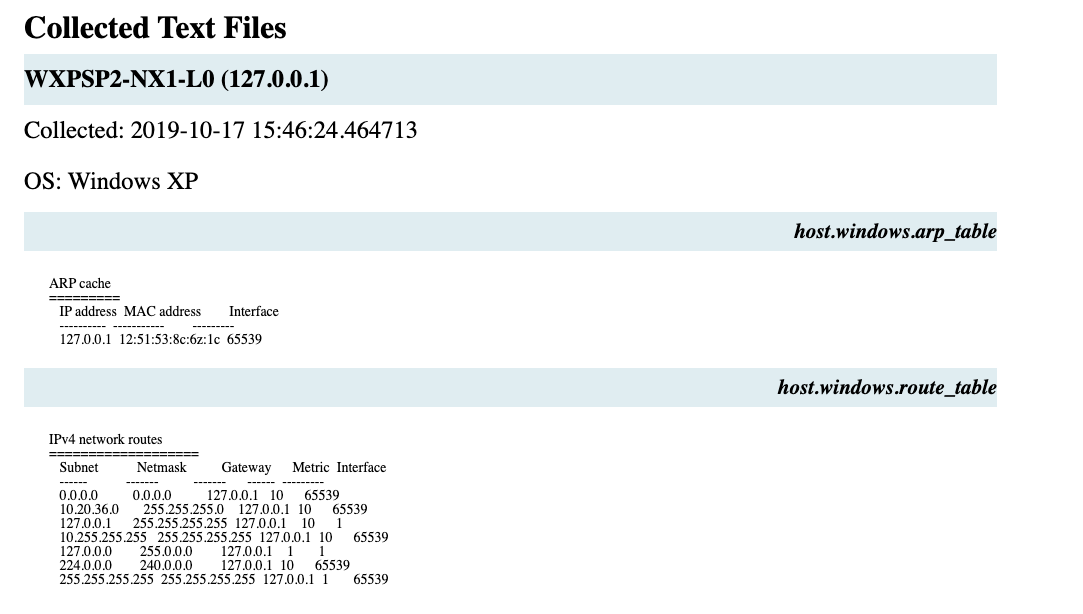
- Hostname and IP Address - Name of the target host and IP address
- Collected - Date and time the screenshot was taken using the format
yyyy-mm-dd hh:mm:ss:fffffffff. - OS - Name of the operating system.
- Description - Description of the file collected.
Collected Evidence Options
The following options are available for generating the Collected Evidence Report.
- File Formats - HTML, PDF, RTF, Word
- Name - Name of Report
- Address Settings - Specify Included Addresses and Excluded Addresses to configure the scope of the report, or leave blank to include all the hosts associated with this project. Hosts with addresses outside the allowable range(s) will not be included in the reported data. Entries may be specified as single addresses (192.168.1.1), dashed entries (192.168.1.1-192.168.1.100), wildcards (192.168.1.*), or using CIDR notation (192.168.1.0/29).
- Cover Logo - If no logo is upload, the Rapid7 logo is used
- Sections - Sections as labeled in the User Interface may not match the exported report.
- Project Summary = Project Summary
- Evidence Summary = Executive Summary
- Evidence Summary Table = Collected Evidence Summary
- Complete Evidence Table = Collected Evidence List
- Collected Screenshots = Collected Screenshots
- Collected Text Files = Collected Text Files
- Options - Include charts
- Email Report - List of comma or semicolon separated addresses to send the report to