Metasploit Framework
The Metasploit Framework is a Ruby-based, modular penetration testing platform that enables you to write, test, and execute exploit code. The Metasploit Framework contains a suite of tools that you can use to test security vulnerabilities, enumerate networks, execute attacks, and evade detection. At its core, the Metasploit Framework is a collection of commonly used tools that provide a complete environment for penetration testing and exploit development. Accessing MSFconsole MSFconsole provides a command line interface to access and work with the Metasploit Framework. The MSFconsole is the most commonly used interface to work with the Metasploit Framework. The console lets you do things like scan targets, exploit vulnerabilities, and collect data.
Accessing MSFconsole on Linux
To run MSFconsole on Linux, open a terminal, cd into the framework directory and type:
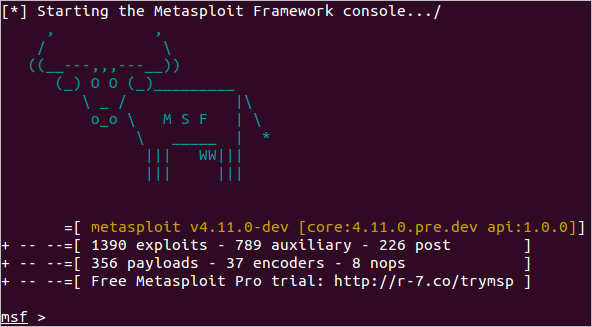
$ ./msfconsoleIf all goes well, you’ll see the following prompt:
However, if this is first time you are accessing the console, you may see an error indicating that you are missing some gems. To fix this error, run bundle install to grab those gems.
To run bundle install, simply type:
$ bundle installAfter you run bundle install, you can try to launch the console again by retyping ./msfconsole.
If you are using a commercial version of Metasploit, such as Metasploit Pro, you can run ./msfpro to launch the console.
Accessing MSFconsole on Windows
If you’re a Windows user, launching MSFconsole is really easy. Go to the Start menu and choose All Programs > Metasploit > Framework > Metasploit Console.
If you prefer to run the console from the command line, open a terminal and run the following commands:
$ cd /metasploit
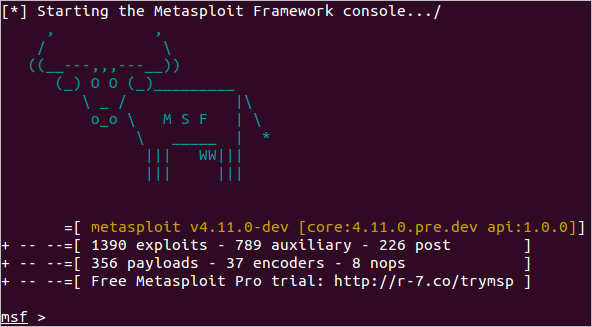
$ console.batIf the console successfully loads, you’ll see the following prompt:
Getting Help for MSFconsole Commands To view help while you are in the console, use the following commands:
- Type
helpto display a list of valid commands for the current mode. While you are in the main mode, the system displays help for the global commands that are available. When you are in the module mode, the system displays the help for the commands and options that are available for the module. - Type
info <module name>to view the options for a module. Finding Modules Modules are the core components of the Metasploit Framework. A module is a piece of software that can perform a specific action, such as scanning or exploiting. Each task that you can perform with the Metasploit Framework is defined within a module.
You can locate modules in the following directory: /path/to/metasploit/apps/pro/msf3/modules if you installed Metasploit using the binaries or /path/to/metasploit-framework-repo/modules if you cloned the repository from GitHub. The modules are categorized by type and then by protocol.
There are a few types of modules. The module type depends on the purpose of the module and the type of action that the module performs. The following are module types that are available in the Metasploit Framework:
- Exploit - An exploit module executes a sequence of commands to target a specific vulnerability found in a system or application. An exploit module takes advantage of a vulnerability to provide access to the target system. Exploit modules include buffer overflow, code injection, and web application exploits.
- Auxiliary - An auxiliary module does not execute a payload. It can be used to perform arbitrary actions that may not be directly related to exploitation. Examples of auxiliary modules include scanners, fuzzers, and denial of service attacks.
- Post-Exploitation - A post-exploitation module enables you to gather more information or to gain further access to an exploited target system. Examples of post-exploitation modules include hash dumps and application and service enumerators.
- Payload - A payload is the shell code that runs after an exploit successfully compromises a system. The payload enables you to define how you want to connect to the shell and what you want to do to the target system after you take control of it. A payload can open a Meterpreter or command shell. Meterpreter is an advanced payload that allows you to write DLL files to dynamically create new features as you need them.
- NOP generator - A NOP generator produces a series of random bytes that you can use to bypass standard IDS and IPS NOP sled signatures. Use NOP generators to pad buffers. Datastore The datastore is a core component of the Metasploit Framework. The datastore is a table of named values that enables you to configure the behavior of the components within the Metasploit Framework. The datastore enables the interfaces to configure settings, the payloads to patch opcodes, and the exploits to define parameters. The datastore also enables the Metasploit Framework to internally pass options between modules.
There are two types of datastores:
- Global datastore - To define a global datastore option, use
setg. All modules will be able to use the datastore option. - Module datastore - To define a module level datastore option, use
set. Only the module that you define the datastore option for can use it.