Working with the Vulnerability Validation Wizard
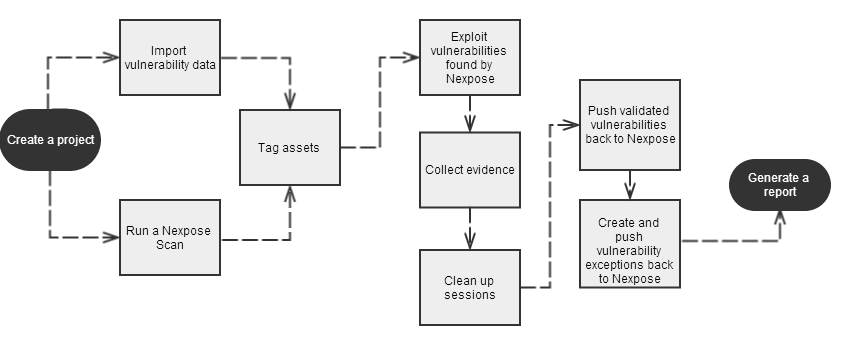
Metasploit Pro simplifies and streamlines the vulnerability validation process. It provides a guided interface, called the Vulnerability Validation Wizard, that walks you through each step of the vulnerability validation process—from importing Nexpose data to auto-exploiting vulnerabilities to sending the validation results back to Nexpose. You can even define exceptions for vulnerabilities that were not successfully exploited and generate a report that details the vulnerability testing results directly from Metasploit Pro.
When you launch the Vulnerability Validation Wizard, you will need to configure the settings for the following tasks:
- Creating a project.
- Scanning or importing Nexpose sites.
- Tagging Nexpose assets. (Optional)
- Auto-exploiting vulnerabilities.
- Generating a report. (Optional) Before You Begin Before you can run the Vulnerability Validation Wizard, you will need to make sure that you have access to a Nexpose instance. You can only validate vulnerabilities with Metasploit Pro if you have Nexpose Enterprise or Nexpose Consultant version 5.7.16 or higher. Please check your Nexpose edition before attempting to use the Vulnerability Validation Wizard.
You must also have at least one site set up in Nexpose. To learn how to set up a site, please view the Nexpose documentation .
Adding a Nexpose Console
You can configure a Nexpose console directly from the Vulnerability Validation Wizard. However, to simplify the vulnerability validation workflow, it is recommended that you globally add the Nexpose Consoles you intend to use prior to launching the wizard.When you globally add a Nexpose Console, it will be accessible to all projects and all users.
To configure a Nexpose Console:
- Select Administration > Global Settings from the Administration menu.
- Find the Nexpose Consoles area.
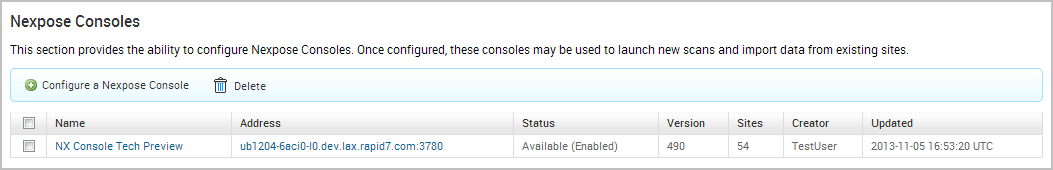
- Click the Configure a Nexpose Console button.
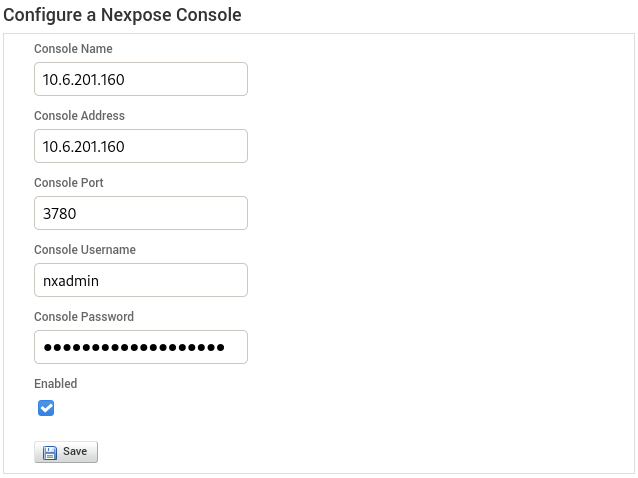
- When the Configure a Nexpose Console page appears, enter the following information:
- Console Address - The IP address to the server that runs Nexpose. You can also specify the server name.
- Console Port - The port that runs the Nexpose service. The default port is 3780.
- Console Username - The Nexpose username that will be used to log in to the console.
- Console Password - The Nexpose password that will be used to authenticate the user account.
- Save the Nexpose Console. Vulnerabilities Imported from Nexpose The Vulnerability Validation Wizard only imports vulnerabilities that have matching Metasploit remote exploit modules that have a ranking of Great or Excellent. Because of this, you may see a large number of vulnerabilities that were discovered, but were not imported into your project because they did not have matching remote exploit modules that meet the required criteria. Vulnerability Validation Wizard Workflow To give you an idea of how you can configure the Vulnerability Validation Wizard, check out the workflow below:
Configuring and Running the Vulnerability Validation Wizard
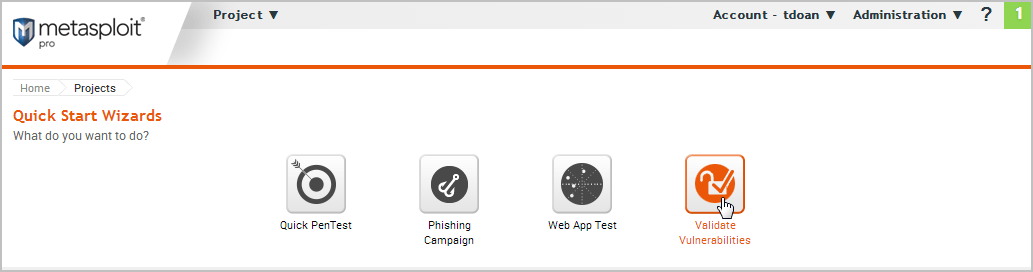
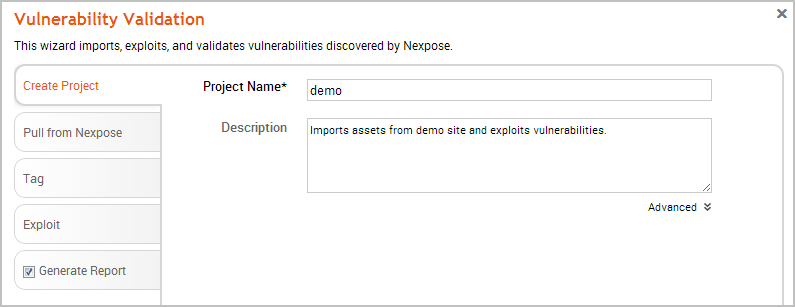
- From the Projects page, click on the Vulnerability Validation widget located under the Quick Start Wizards area. The Validate Vulnerabilities Wizard opens and displays the Create Project page.
- In the Project Name field, enter a name for the project. The project name can contain any combination of alphanumeric characters, special characters, and spaces. You can also provide an optional description for the project, which typically explains the purpose and scope of the test.
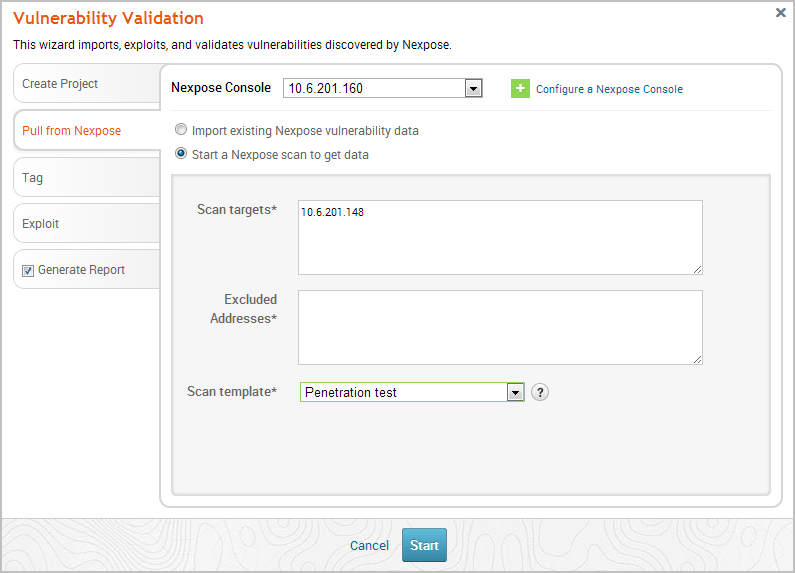
- Click on the Pull from Nexpose tab. The Nexpose Consoles page appears.
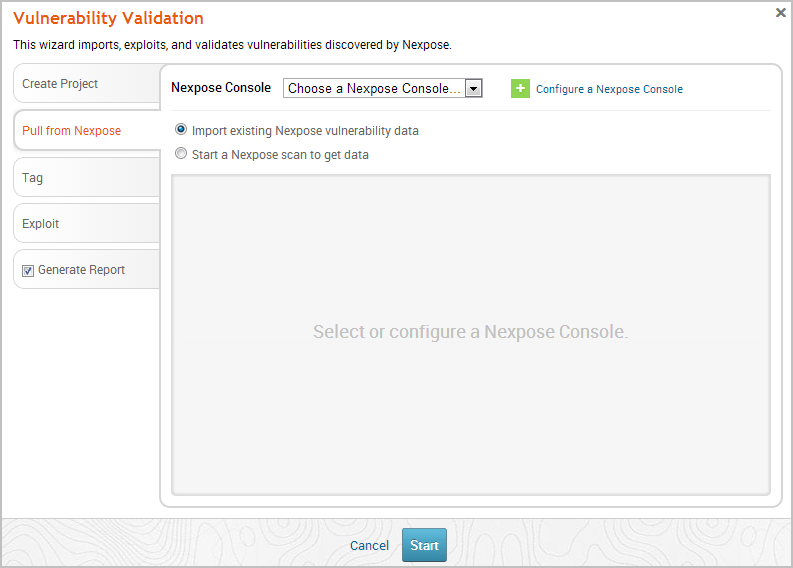
- Click the Nexpose Console dropdown and select the console that you want to pull data from. If there are no consoles available, you can click the Configure a Nexpose Console link to add one.
- After you select a console, you can choose whether you want to run a Nexpose scan or import existing Nexpose data. Depending on the option you choose, the wizard will show the appropriate configuration page.
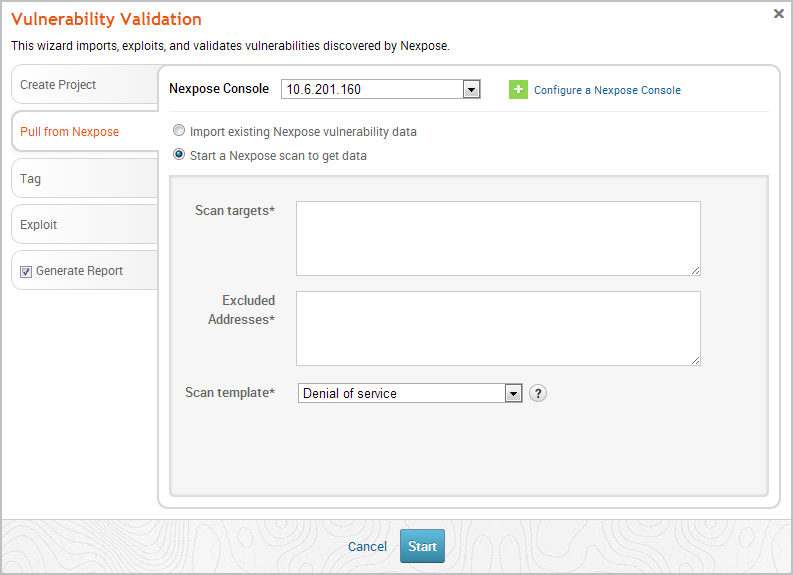
- Select the Start a Nexpose Scan to get data option.
- Enter the host addresses, or assets, that you want to scan in the Scan targets field. You can enter a single IP address, a comma separated list of IP addresses, an IP range described with hyphens, or a standard CIDR notation.
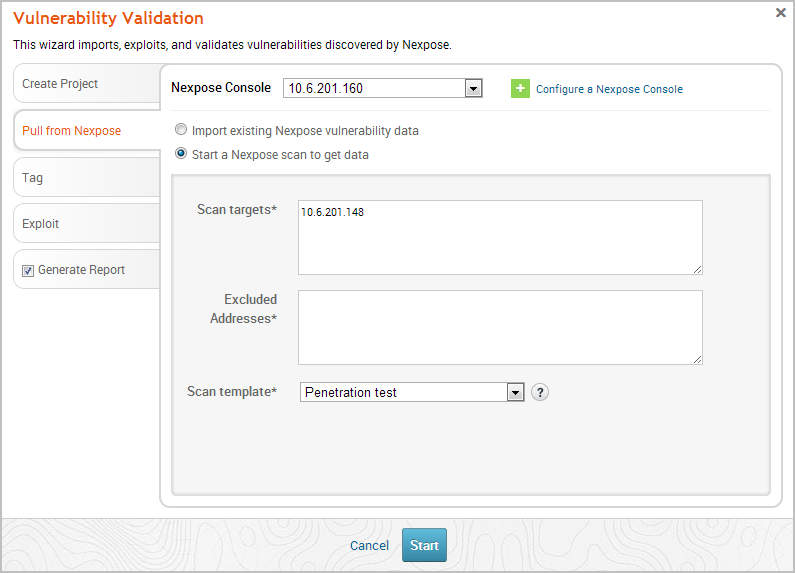
- Click the Scan template dropdown and select the template you want to use.
A scan template is a predefined set of scan options. There are a few default ones that you can choose from. For more information on each scan template, please see the Nexpose documentation .
- Click the Tag tab.
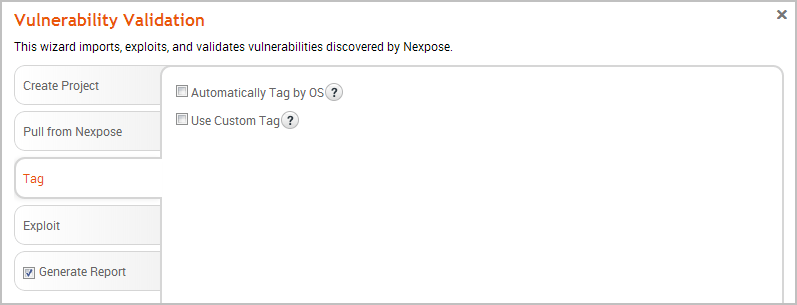
- Select the Automatically tag by OS option if you want to tag each host with its operating system.
If enabled, hosts will be tagged with os_linux or os_windows.
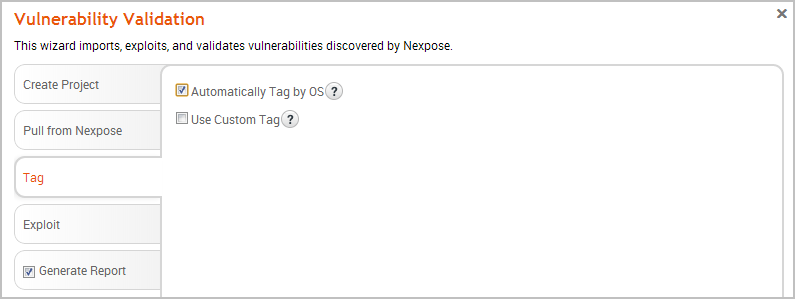
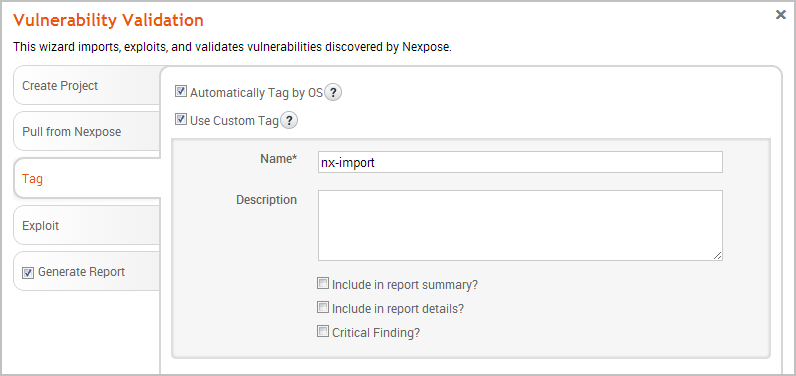
- Select the Use custom tag option if you want to tag each host with a user-defined tag. If this option is enabled, the Vulnerability Validation Wizard displays the fields and options that you can use to create a custom tag.
- After you configure the tagging options, click on the Exploit tab. The Auto-Exploitation page appears.
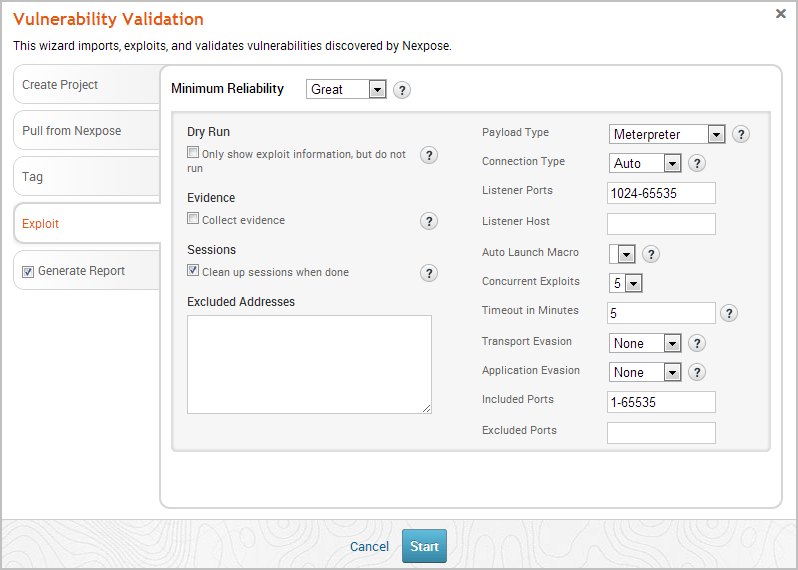
-
Click the Minimum Reliability dropdown and choose the module ranking you want to use. You should use Great or Excellent.
-
Use any of the following options to configure exploitation settings:
- Dry Run - Prints a transcript of the exploits in the attack plan without running them.
- Collect Evidence - Collects loot, such as screenshots, system files, passwords, and configuration settings from open sessions.
- Clean Up Sessions - Closes all sessions after all tasks have run.
- Payload Type - Specifies the type of payload that the exploit will deliver to the target. Choose one of the following payload types:
- Command - A command execution payload that enables you to execute commands on the remote machine.
- Meterpreter - An advanced payload that provides a command line that enables you to deliver commands and inject extensions on the fly.
- Connection Type - Specifies how you want your Metasploit instance to connect to the target. Choose one of the following connection types:
- Auto - Automatically uses a bind connection when NAT is detected; otherwise, a reverse connection is used.
- Bind - Uses a bind connection, which is useful when the targets are behind a firewall or a NAT gateway.
- Reverse - Uses a reverse connection, which is useful if your system is unable to initiate connections to the targets.
- Listener Ports - Defines the ports that you want to use for reverse connections.
- Listener Host - Defines the IP address you want to connect back to.
- Auto Launch Macro - Specifies the macro that you want to run during post-exploitation.
- Concurrent Exploits - Specifies the number of exploit attempts you want to launch at one time.
- Timeout in Minutes - Defines the number of minutes an exploit waits before it times out.
- Transport Evasion - Choose from the following transport evasion levels:
- Low - Inserts delays between TCP packets.
- Medium - Sends small TCP packets.
- High - Sends small TCP packets and inserts delays between them.
- Application Evasion - Adjusts application-specific evasion options for exploits involving DCERPC, SMB and HTTP. The higher the application evasion level, the more evasion techniques are applied.
- Included Ports - Defines the specific ports you want to target for exploitation.
- Excluded Ports - Defines the specific ports you want to exclude from exploitation.
-
Click the Generate Report tab if you want to include an auto-generated report at the end of the vulnerability validation test. If you do not want to include a report, deselect the Generate Report option and skip to the last step.
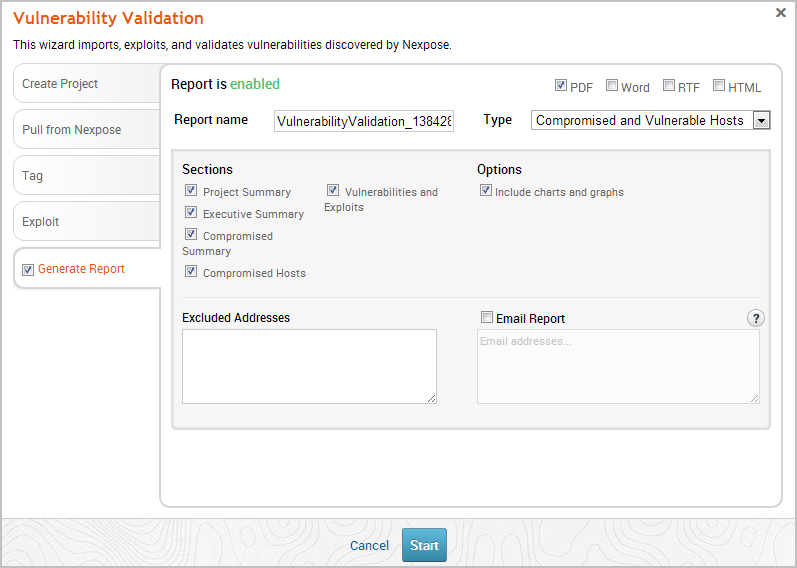
- Enter a name for the report in the Report Name field, if you want to use a custom report name. Otherwise, the wizard uses an auto-generated report name.
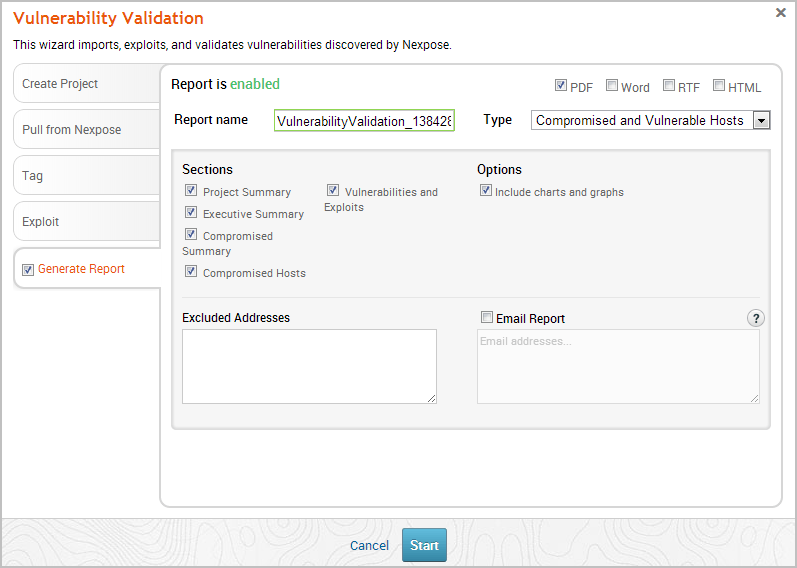
- Select whether you want to generate the report in PDF, RTF, or HTML. PDF is the preferred and default format.
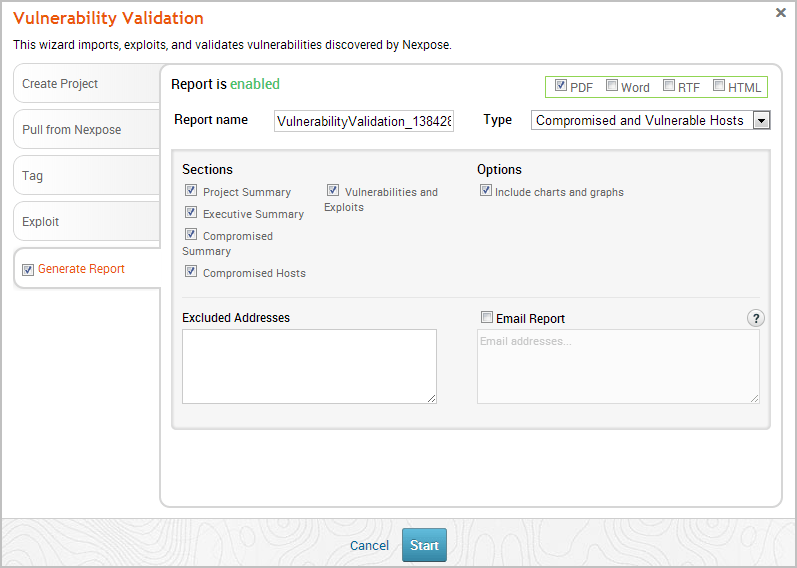
- Click the Type dropdown and select the report type you want to generate. You can choose the Audit report or the Compromised and Vulnerable Hosts report.
- From the Sections area, deselect any sections you do not want to include in the report. Skip this step if you want to generate all the report sections.
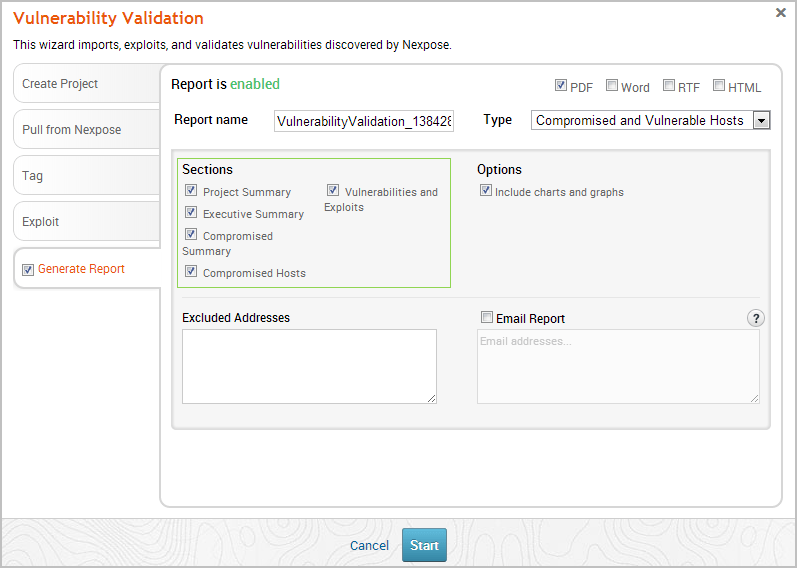
- Enter any hosts, or assets, whose information you do not want included in the report in the Excluded Addresses field. You can enter a single IP address, a comma separated list of IP addresses, an IP range described with hyphens, or a standard CIDR notation.
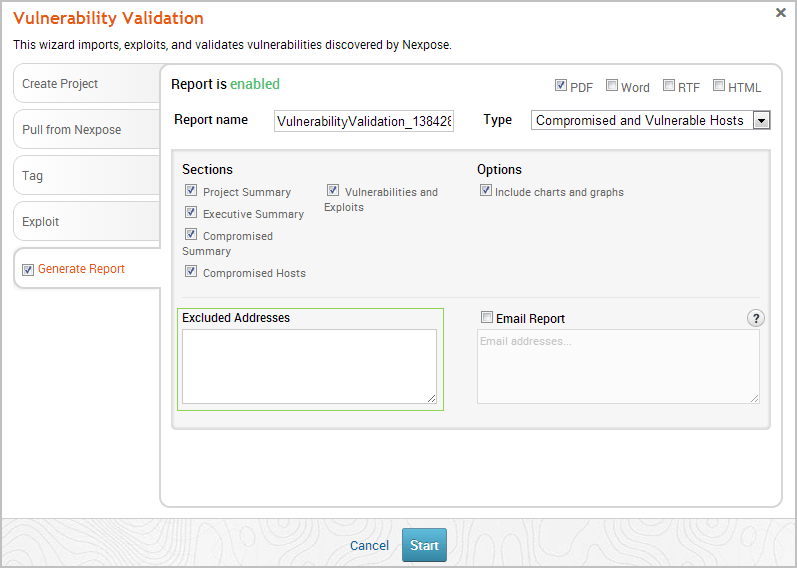
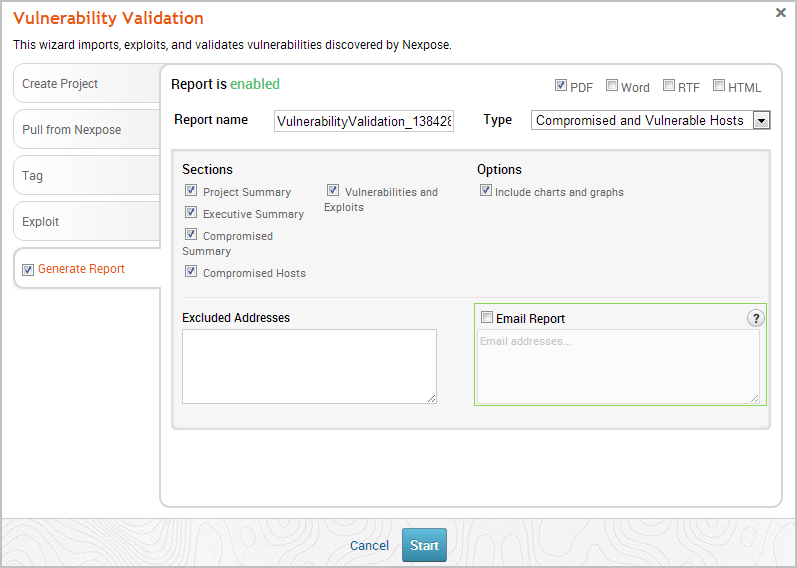
- Select the Email Report option if you want to email the report after it generates. If you enable this option, you need to supply a comma separated list of email addresses.
If you want to email a report, you must set up a local mail server or email relay service for Metasploit Pro to use. To define your mail server settings, select Administration > Global Settings > SMTP Settings.
- Click the Launch button. The Findings window appears and shows the statistics for the test.
Readiness States for matched exploit modules are reported on the Remote exploit matches table of the Findings window.