Scanning a load balancer
NOTE
This guide explains why scanning through a load balancer is not recommended. Examine the following figures and steps to accommodate scanning when a load balancer is deployed in your environment.
Load balancers are commonly used in modern day networking environments, so it’s important to be mindful of how they work in association with Nexpose. As the load balancer distributes traffic among your servers, you must ensure that your scans do not pick up all the resulting dynamically assigned assets.
This concept is illustrated in the following diagram:
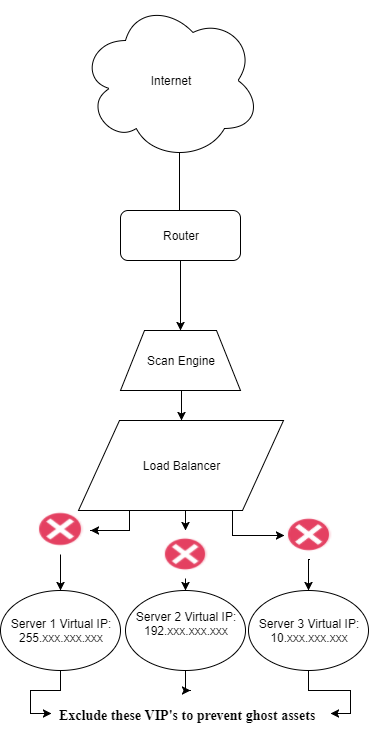
While the load balancer itself can be scanned for vulnerabilities, you should avoid scanning through the load balancer. Scan results will vary depending on the the communication route that is utilized when the scan is run.
To avoid this, exclude the virtual IPs of the servers and strictly limit your scanned IPs to the load balancer itself:
- In your Security Console Home screen, browse to the Sites window. Click the icon under the Edit column for the site you need to configure. This will open the Site Configuration screen.
- Click the Assets tab.
- Under the Exclude dropdown on the right side of the screen, specify all virtual server IPs in the field under Assets.
- Click Save when finished.
TIP
We also suggest putting your scan engine on the same network segment as the load-balanced servers to avoid any routing issues.