Network Sensor for AWS Requirements
The Rapid7 Network Sensor (Insight Network Sensor) for AWS deployment requires a provisioned virtual host and the necessary network infrastructure to receive your network traffic. The following section will cover all host system and networking requirements so that you are prepared for the deployment phase.
Before you start the installation process, make sure that you have configured the following:
| Name | Description |
|---|---|
| VPC ID | The VPC where the sensor will be deployed. |
| SSH KeyPair | A KeyPair that can be used to access the sensor shell if required. |
| Command Platform (Insight Platform) install token for sensor | A token to identify the new sensor to the Command Platform (Insight Platform). You can get this from Command Platform (Insight Platform) Collection Data Management . |
| Platform Comms Subnet | Allows the sensor to communicate with the Command Platform (Insight Platform). You may use an existing subnet or create a new one. |
| Platform Comms Security Group | Allows outbound https. You may use an existing Security Group or create a new one. |
| Mirror Subnet | A private subnet for Mirror Traffic. You may use an existing subnet or create a new one. |
| Mirror Security Group | Allows UDP 4789 from VPC. You may use an existing Security Group or create a new one. |
Configure your Network Infrastructure
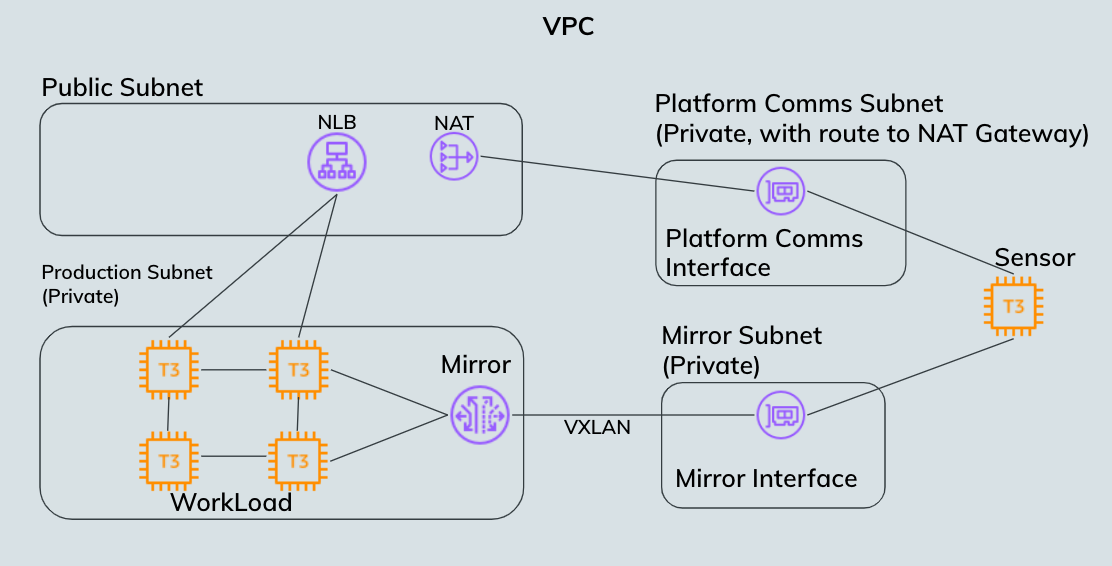
To help you visualize the network infrastructure, a simplified VPC with workload servers and sensor is shown below.
Workload
Workloads traffic is routed to servers in a private Production Subnet from a Load Balancer in a public subnet. A sensor is installed in the VPC, with 2 Network Interfaces (NICs). One NIC is in the Platform Comms subnet, a private subnet, with a route to a Network Address Translation (NAT). The second NIC is in a private Mirror Subnet. It does not require any routing to gateways. Interfaces on the Workloads server are mirrored to the Mirror Interface (Mirror Target) on the Sensor.
Mirrored Network Interfaces
The Network Sensor for AWS requires 2 network interfaces. One NIC is used for communication with the Command Platform (Insight Platform). This is referred to as the Platform communications NIC. The second NIC is used to receive Mirror Traffic and is referred to as the Mirror Traffic NIC.
Configure your NICs on different subnets
AWS advises against configuring 2 NICs on an instance in the same subnet. By using 2 NICs and subnets, you can isolate mirror traffic from production or platform communication traffic. See the AWS documentation for more details: https://docs.aws.amazon.com/AWSEC2/latest/UserGuide/using-eni.html#best-practices-for-configuring-network-interfaces .
Network Interface Requirements
The following are the properties required for NIC configuration on the Network Sensor EC2 instance:
| NIC Name | Description | Subnet Properties | Security Group |
|---|---|---|---|
| Platform Comms | Facilitates communication with the Command Platform (Insight Platform) for configuration and payload upload. | Has a route to the NAT gateway. ACL default rule that allows any traffic. | Allow outbound https (443) to the internet. |
| Mirror Traffic | Receives Mirror Traffic for analysis. | ACL default rule that allows any traffic. | Allow inbound from the VPC on UDP port 4789. |
Once you have configured your VPC and ensured that you have everything listed above, you are ready to move on to the deployment phase.