IntSights Splunk App for Splunk SOAR Installation and Configuration
Describes how to install and configure the IntSights Splunk App for Splunk SOAR, an external app. All the relevant information can be found at https://github.com/splunk-soar-connectors/intsights
Before you can use the external app with Rapid7 Digital Risk Protection (Threat Command) you need to add the app.
Add external app
Before using an external app, you must add it. There are two parts to adding an app:
- Your admin must enable the app for you to add.
- After that, you add the external app.
To add an external app:
- From the main menu, select Automation > Integrations.
- From the Integrations page, click External.
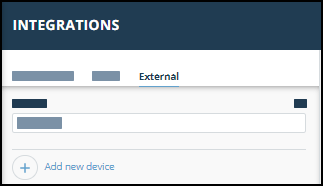
- Click Add new device.
- Select the Device type.
A default name is added. If the external device to add isn’t displayed, ask your admin to enable it for you. - Click Add.
The new device is added.
Install the app
Describes how to install the app.
To install the app:
- Download the IntSights Splunk App TGZ file from https://splunkbase.splunk.com/app/6031/
- Log into the Phantom console.
- In the top left of the screen, select Apps from the drop-down menu.
- Click INSTALL APP to install the downloaded TGZ module into Phantom.
Create an asset for the app
Describes how to configure an asset. Before you begin, you need the Digital Risk Protection (Threat Command) API key and account ID, as described in API key and account ID. To create an asset for the app in Phantom:
- Log in to the Phantom platform.
- Navigate to the Home dropdown and select Apps.
- Search the IntSights Splunk App from the search box.
- Click CONFIGURE NEW ASSET.
- Navigate to the Asset Info tab and enter the Asset name and Asset description.
- Navigate to the Asset Settings tab.
- Paste the API Key and Account ID that was created from Digital Risk Protection (Threat Command).
- Save the asset.
- It is recommended to test the connectivity of the Phantom server to the Digital Risk Protection (Threat Command) instance by clickingTEST CONNECTIVITY.