Lateral Movement
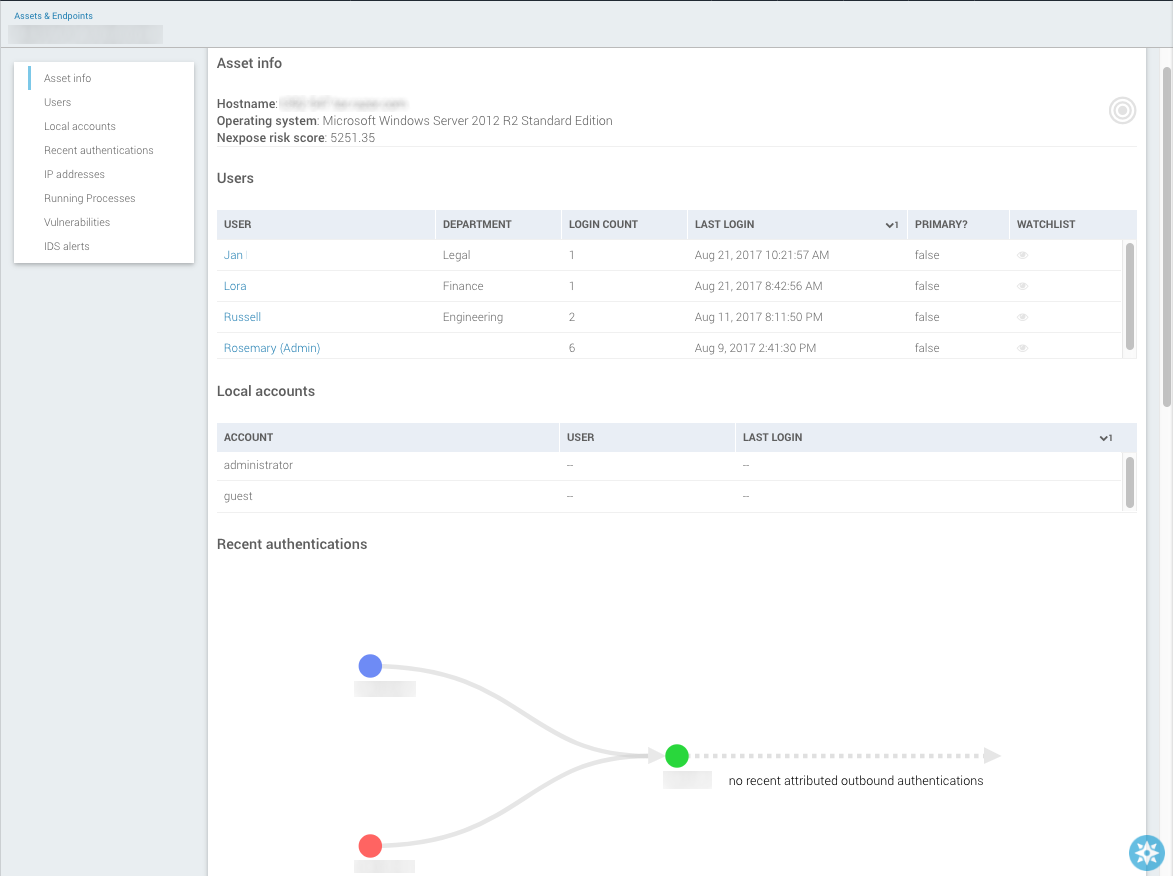
Authentication activity on an endpoint, whether using local or domain accounts, includes the source machine and account from which the authenticator came. With this information, SIEM (InsightIDR) can aggregate and present visualizations displaying exactly where users came from when logging into any particular asset on the network and which assets users authenticated to next from that asset.
Attackers move laterally when they jump from one endpoint to another to infiltrate a network without informing the Active Directory. This is a common attacker methodology, including pass-the-hash attacks. Lateral movement cannot be detected simply by reading Active Directory logs – it requires visibility into the endpoints.
View Lateral Movement
When you view an individual asset page, you may see a section for “Recent Authentication”. This graph allows security administrators to retrace the steps of any lateral movement as the user hops from machine to machine across the environment.
See Local accounts for more information.
Lateral Movement Detections
You can configure Lateral Movement detection rules depending on your environment. To do so, go to Detection Rules > Legacy UBA Detection Rules and scroll to the various Lateral Movement rules. In the Rule Action column, select the action that you want to occur when the rule logic is met.
By default, the Rule Action for the following detection rules is set to Creates Investigations:
- Lateral Movement - Administration Impersonation - A user has authenticated to an administrator account.
- Lateral Movement - Domain Credentials - A domain account has attempted to access several new assets in a short period of time.
- Lateral Movement - Local Credentials - A local account has attempted to access several assets in a short period of time.
- Lateral Movement - Service Account - A service account is authenticating from a new source asset.
- Lateral Movement - Watched User Impersonation - A user has authenticated to a watched user’s account.