Users and Accounts
A user is the container that holds all the correlated account information from SIEM (InsightIDR). An account is something that a user logs into, such as Okta, Active Directory or an Office 365 user token. If a user has multiple accounts, SIEM (InsightIDR) automatically identifies this information and builds dedicated pages for each and every user, asset, and process observed in your environment. There are several types of identified user accounts:
Additionally, you can add risky users to a watchlist.
View Users and Accounts
You can click a username to go to that user’s page or you can use the global search bar at the top of the interface to search for a particular user, account, asset, or process.
On the Users & Accounts page, you will see several metrics about the different kinds of user accounts.
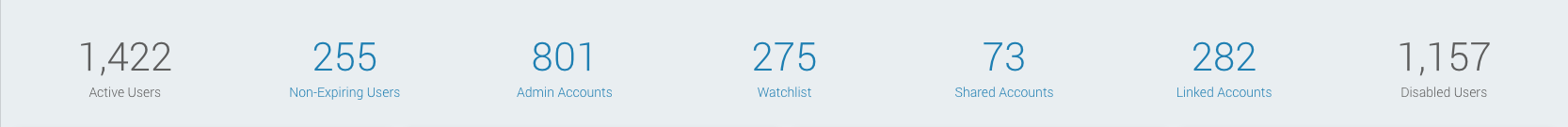
- Active Users: This number of active users SIEM (InsightIDR) has discovered in your organization.
- Directory User This user was directly collected from a directory service.
- Observed User This user was observed from logs collected by SIEM (InsightIDR) that are not associated with known directory users.
Although SIEM (InsightIDR)‘s primary way of detecting users is from your identity and LDAP event sources, it will also find users in other places, such as cloud services, VPN, and ingress activity.
The number of active users is the total number of active user accounts, not including Service Accounts or disabled users.
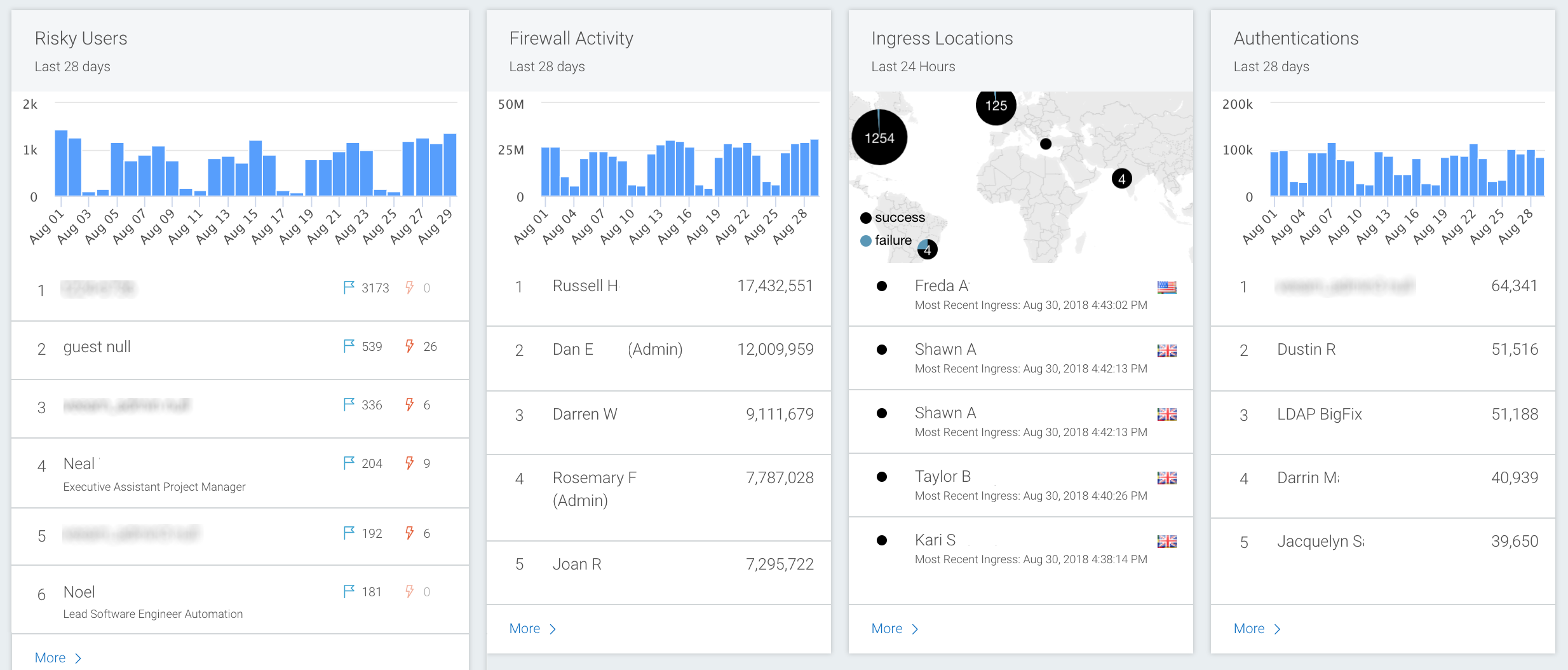
The Users & Accounts page also shows data provided by various event sources in the context of user activity, such as graphical information about your risky users and virus alerts per user. Additionally, the page shows data related to:
- Firewall activity
- Intrusion detection systems (IDS)
- Authentications
- Web proxies
- Unique processes
- Ingress locations
Note that many of these graphs can be filtered down to a more specific data set. For example, Firewall Activity can be filtered to show only Outbound Denies.
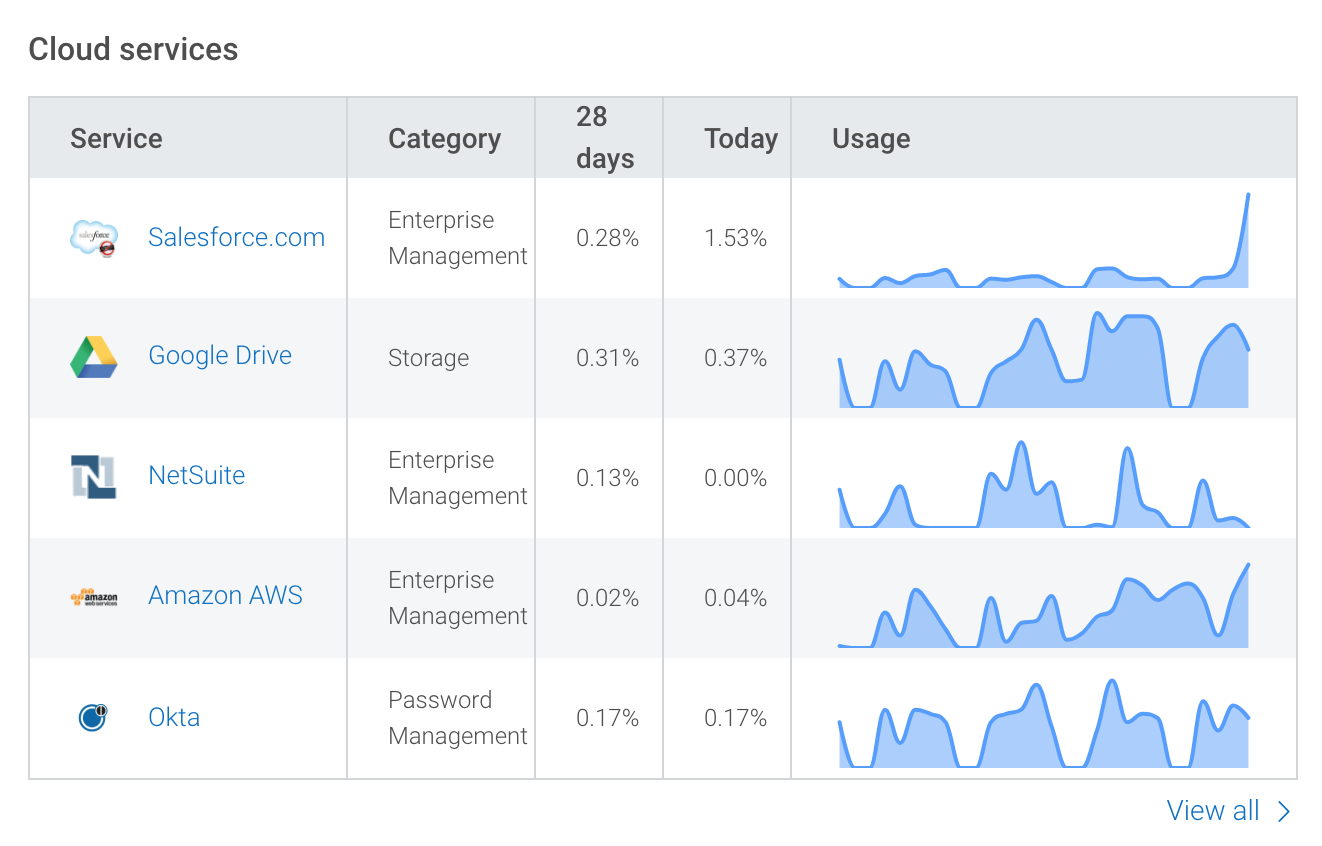
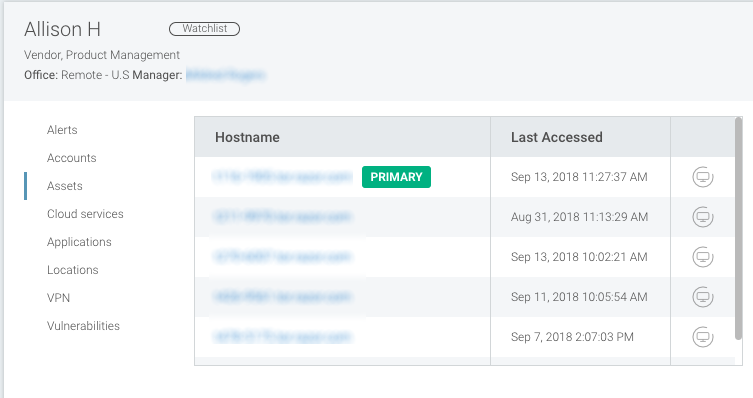
On any individual user’s page, you will see specific information about Cloud Services, locations, assets, and more.
Vulnerabilities on user’s assets
If you are using SIEM (InsightIDR) with Vulnerability Management (InsightVM), each asset for the user will have a count of the vulnerabilities active on that asset. You can click on the count to see complete vulnerability information for the asset in Vulnerability Management (InsightVM).
Link to identity data in Attack Surface Management
If you use both SIEM (InsightIDR) and Attack Surface Management, the User details page in SIEM (InsightIDR) includes a link to Identities in Attack Surface Management. Use this link to navigate from a user in SIEM (InsightIDR) to the corresponding Identity in Attack Surface Management. From there, you can review related identity data, such as multi-factor authentication (MFA) status, account posture, and other associated context.
Query logs related to a user
On the User Details page, select a log or log set from the Search Related Logs section to run a query on a user’s activity in that log set.
Selecting a related log set will open Log Search, automatically select the log set from the log set panel, add this user to the query bar, and run the query.
Note: Queries created using the Search Related Logs buttons will default to a time range of the past hour.
Related Alerts
The Related Alerts table provides an overview of alerts that were generated for the same asset on the User Details or Asset Details page. You can views all related alerts for the user or asset. Alternatively, you can switch to all related alerts for the user or asset, based on actor, by using the Include Actor toggle. You can also filter by time range. Click View to open Alerts in a new tab.
Local Accounts
Any local accounts on an endpoint become visible as a result of the Rapid7 Agent (Insight Agent).
Local accounts for an asset are presented on that asset’s details page, and Lateral Movement from asset to asset using local accounts are displayed on the lateral movement graph for each asset.
Ingress Authentication
You can view authentication attempts on the Ingress Locations map, which is available from the Users and Accounts page or the SIEM (InsightIDR) Home page. Authentication events are sent from VPN, Cloud Services, or Universal Ingress event sources and appear on your map as success, failure, or unspecified events:
- Success - successful authentication attempts.
- Failure - failed authentication attempts.
- Unspecified - authentication events that are unspecified because the event source does not provide enough information for SIEM (InsightIDR) to determine whether an authentication attempt succeeded or failed.
Primary Assets
You may see a primary asset tag on a User Details page. This indicates which user account primarily uses the asset. Assets without tags are likely shared or linked accounts. For more information on how this tag is determined, see User Attribution.
Export User Data
You can export data about a user from an individual user page. Search or go to the User Details page. Click the Download button at the top right of the page, which generates a PDF that will download to your local machine.