Microsoft SCCM - Automation-Assisted Patching
Feature availability notice
Rapid7 no longer offers Built-in Automation Workflows for new Vulnerability Management (InsightVM) customers. This feature is available to eligible Vulnerability Management (InsightVM) users only. If interested in this feature, see our Exposure Command offering .
This article details the Automation-Assisted Patching with Microsoft SCCM workflow offered with the Automation feature in InsightVM.
REMINDER
Vulnerability Management (InsightVM) automation workflows require an installed and activated orchestrator in order to communicate with your external tools.
If you still need to deploy an orchestrator, see the orchestrator help page for installation instructions.
This content covers the following topics:
- Goal
- How it Works
- Limitations
- Workflow Process In-Depth
- Vulnerability Management (InsightVM) Workflow Configuration Instructions
- Troubleshoot
- Resources
Goal
This workflow is designed for Vulnerability Management (InsightVM) users who want to leverage their Microsoft System Center Configuration Manager (SCCM) tool to ease the vulnerability management process with automation assistance.
How it Works
This workflow consumes vulnerability and asset information from Vulnerability Management (InsightVM) in order to form queries that check SCCM for relevant patches and assets. If the workflow finds matching patches and assets, it creates and stages a pair of SCCM entities (a Software Update Group and a Device Collection) that SCCM can deploy.
Trigger Behavior
Workflow triggers respond when the Insight platform receives new vulnerability assessment data from your environment. In other words, newly configured workflows will not initiate based on the current state of your network, even if that current state falls within the trigger scope you have defined.
In this context, workflow triggers respond to the data uploads that consist of completed vulnerability scans initiated by your Security Console and completed vulnerability assessments reported by your Rapid7 Agents (Insight Agents). The Insight platform checks the trigger conditions associated with your workflows when these data uploads take place and initiates the workflows that qualify.
NOTE
If you experience delays or stops in trigger events, it could be due to platform communication issues. Check the Configure communications with the Insight platform page to verify that your whitelist settings are correct.
Limitations
This workflow operates under the following limitations:
- The workflow only supports Microsoft vulnerabilities and their respective patches.
- The workflow can only implement patches based off content available in SCCM.
- Vulnerability Management (InsightVM) will not take action if identified vulnerabilities do not have a relevant patch in SCCM.
- Assets included in the workflow scope in Vulnerability Management (InsightVM) must also correlate to available assets (referred to as “devices”) in SCCM.
- If Vulnerability Management (InsightVM) includes assets that SCCM is not aware of, the workflow will not take action for those assets.
- Assets identified as vulnerable by Vulnerability Management (InsightVM) must also be identified as vulnerable by SCCM or the workflow will not take action.
Workflow Process In-Depth
This workflow proceeds through the following steps in order to meet its goal:
- Goal
- How it Works
- Limitations
- Workflow Process In-Depth
- Vulnerability Management (InsightVM) Workflow Configuration Instructions
- Troubleshoot
- Resources
Trigger the Workflow Based on Asset and Vulnerability Filters
The asset and vulnerability filters you configure during the workflow wizard serve together as the trigger for initiating the workflow. When qualifying data is detected on a state change, Vulnerability Management (InsightVM) packages this trigger data into an artifact. This artifact includes general information about the trigger data, such as descriptions, timestamps, and asset data.
Query SCCM with Trigger Data
The workflow then queries SCCM to see if the workflow name you specified in the configuration wizard matches an existing Software Update Group name.
TIP
The workflow uses its own Vulnerability Management (InsightVM) name to find possible matches for both a Software Update Group and a Device Collection in SCCM. For example, if you name your workflow “My Workflow” during the configuration wizard, the workflow looks for a Software Update Group and Device Collection of the same name.
Note that neither the Software Update Group nor the Device Collection need to already exist prior to the configuration for this workflow to complete successfully. At this stage, if the workflow does not find a matching Software Update Group, it will create a new one for you.
With either an existing or new Software Update Group in place, the workflow queries the SCCM server for software updates based on each Software Update ID associated with the vulnerabilities in the workflow trigger:
- If software updates are found, the workflow adds them to the Software Update Group and logs an artifact to reflect this.
- If software updates are not found, the workflow creates an artifact to note this.
The workflow then determines if the workflow name you specified in the configuration wizard matches an existing Device Collection in SCCM:
- If a matching Device Collection exists, the workflow queries SCCM for the asset hostnames included in the workflow trigger. The workflow adds matching SCCM hostnames that are not already part of the existing Device Collection and logs an artifact. If the hostname is not found in SCCM, the workflow creates an artifact to note this.
- If a matching Device Collection does not exist, the workflow creates a new Device Collection in SCCM based on the assets included in the workflow trigger. Just as before, the workflow adds matching SCCM hostnames to the new Device Collection and logs an artifact. If the hostname is not found in SCCM, the workflow creates an artifact to note this.
SCCM Stages Completed Software Update Group and Device Collection for Deployment
The workflow completes when the Software Update Group and Device Collection are staged in SCCM.
NOTE
The workflow does not deploy software updates itself. SCCM is ultimately responsible for deploying software updates after the Software Update Group and Device Collection have been staged.
Vulnerability Management (InsightVM) Workflow Configuration Instructions
To configure a new workflow using the Automation-Assisted Patching with Microsoft SCCM template in Vulnerability Management (InsightVM), follow these steps:
Configure the Workflow Trigger
First, you need to configure the trigger conditions that will initiate the workflow.
To start the wizard and configure your workflow trigger:
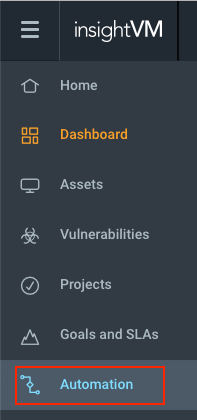
- In Vulnerability Management (InsightVM), click the Automation tab on your left navigation menu.
- On the “Automation” page, click + New Automation in the upper right corner. The automation configuration wizard appears.
- Select Workflow and click Continue.
- Click the Vulnerability trigger type radio button.
- The Automation-Assisted Patching with Microsoft SCCM template requires this trigger type.
- Apply an asset filter and a vulnerability filter to refine the scope of your trigger. Click Continue when ready.
- These filters determine what assets the workflow sends to SCCM and what vulnerabilities on those assets need to be remediated.
- Select the Automation-Assisted Patching with Microsoft SCCM workflow template from the dropdown list. A preview of all individual workflow steps will appear. Click Continue at the bottom of this step list when ready.
Select or Configure a Connection
Next, you need to select an existing connection to your SCCM tool, or configure a new one for the workflow to use.
To create a new connection:
- Select New Connection from the dropdown list. The connection creation form appears.
- Give your new connection a name. You will be able to select this connection in future workflow wizards.
- Select the orchestrator that has access to your SCCM tool from the dropdown list.
- Select an existing credential associated with your SCCM tool from the dropdown list, or click Create New Credential to configure a new one.
- In the context of Vulnerability Management (InsightVM) automation workflows, a “credential” is a username and password pair for an account that you would use to access your SCCM software.
NOTE - Credential account requirements
To run this workflow, your credential account must have administrator privileges and read/write access on the SCCM software.
- In the “Server IP” field, enter the IP address for the Windows server that hosts the SCCM software.
- If you don’t know this address, open a command prompt on the Windows server and run
ipconfig. The address will appear next toIPv4 Address.
- If you don’t know this address, open a command prompt on the Windows server and run
- This workflow uses the Windows Remote Management (WinRM) protocol to communicate with your SCCM server. In the “WinRM Port” field, enter a corresponding port number.
- By default, WinRM listens on ports 5985 and 5986. Vulnerability Management (InsightVM) currently only supports port 5986 for HTTPS/TLS.
TIP
Although this field is technically not required to save your connection, it defaults to port 5986 if left blank.
- In the “SCCM Path” field, enter the absolute path to the SCCM AdminConsole binaries.
- By default, this path is
C:\Program Files (x86)\Microsoft Configuration Manager\AdminConsole\bin, but note that this location can vary depending on how SCCM was originally installed. Check with your SCCM administrator to confirm that your SCCM path is correct.
- By default, this path is
- In the “Site Path” field, enter the site code of your SCCM server.
- SCCM site codes are often composed of three characters. You can determine your site code by navigating to Administration > Site Configuration > Sites in your SCCM Admin Console.
- Click Save Connection when finished.
With your connection selected, click Continue.
Name and Activate Your Workflow
Now that you’ve configured your workflow trigger and connection, give your workflow a name so that you can identify it in your “Workflows” table. Click Activate to complete the workflow wizard.
Your workflow is ready!
You should now have successfully configured a workflow with the Automation-Assisted Patching with Microsoft SCCM template.
Troubleshoot
See the Troubleshoot Microsoft SCCM Connection section of the Microsoft SCCM Automation (InsightConnect) Help page for common troubleshooting scenarios and solutions.
Resources
- Microsoft SCCM documentation - https://docs.microsoft.com/en-us/sccm/core/understand/introduction