Cisco ACS
Cisco Access Control System (ACS) is one of Cisco’s end-of-life products that enhanced visibility and controlled the access of your users across your domain. Read more about the product here: https://www.cisco.com/c/en/us/products/security/secure-access-control-system/index.html
You can configure the Cisco appliance to send VPN data to SIEM (InsightIDR).
SIEM (InsightIDR) only supports Cisco ACS versions 5.x and higher.
Configure Cisco ACS
You must configure the appliance to send syslog to SIEM (InsightIDR).
To configure syslog forwarding:
- Sign in to your Cisco Secure ACS console.
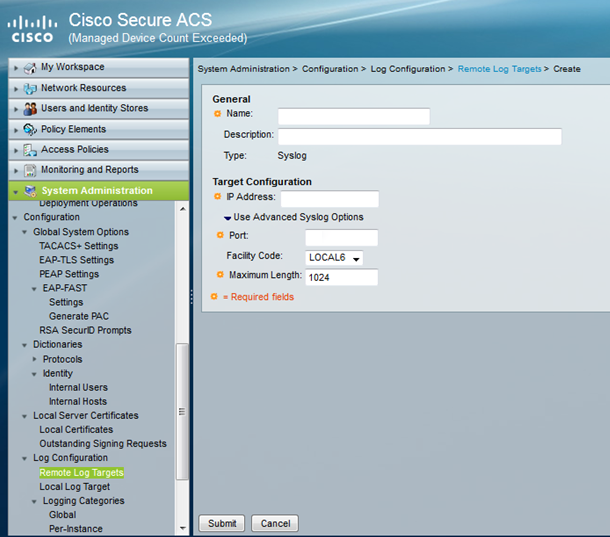
- Expand System Administrator > Log Configuration and select the Remote Log Targets page.
- Click the Create button to create a new syslog target. The log type should automatically be “Syslog.”
- Provide a name for the syslog target, for example, “SIEM (InsightIDR) Collector.”
- Enter the IP address of your SIEM (InsightIDR) Collector in the “IP Address” field.
- Enter the unique port on the Collector that will receive the VPN events.
- Enter the maximum length of the remote log target messages.
- Click the Submit button to save the configuration.
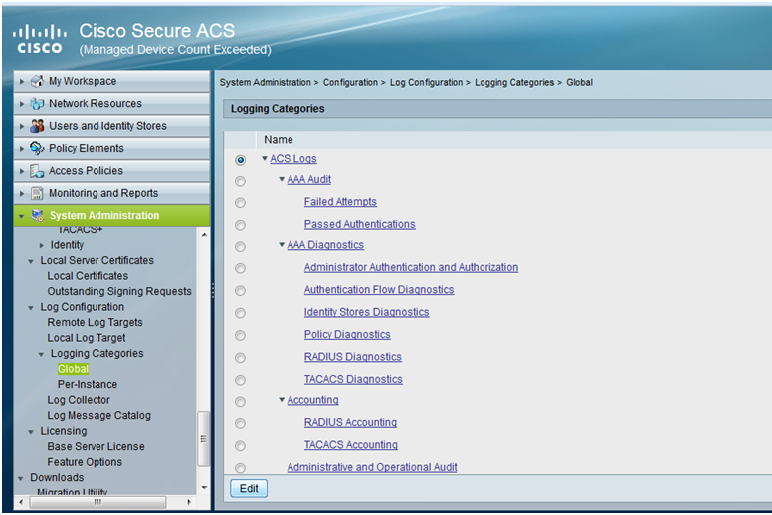
- From the left menu, select Logging Categories > Global.
- Select the ACS Logs radio button at the top.
- Click the Edit button at the bottom.
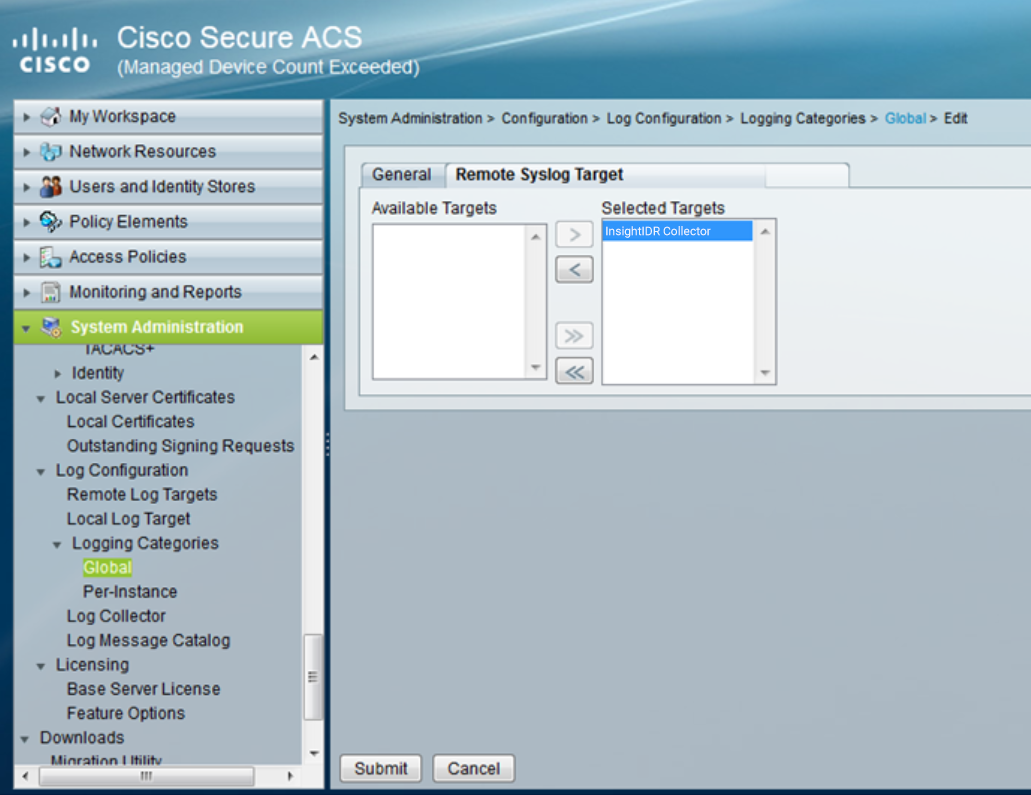
- Select the Remote Syslog Target tab.
- In the “Available Targets” list, select the SIEM (InsightIDR) Collector you identified previously and click the > button to move it into the “Selected Targets” list.
- Click the Submit button to save the configuration.
For additional, detailed instructions, and examples of logs, you can read more about this configuration here: https://community.cisco.com/t5/security-documents/acs-5-x-configuring-the-external-syslog-server/ta-p/3143143
Configure SIEM (InsightIDR) to collect data from the event source
After you complete the prerequisite steps and configure the event source to send data, you must add the event source in SIEM (InsightIDR).
To configure the new event source in SIEM (InsightIDR):
- From the left menu, go to Data Collection and click Setup Event Source > Add Event Source.
- Do one of the following:
- Search for Cisco ACS VPN in the event sources search bar.
- In the Product Type filter, select VPN.
- Select the Cisco ACS VPN event source tile.
- Choose your collector and event source. You can also name your event source if you want.
- Choose the timezone that matches the location of your event source logs.
- Optionally choose to send unparsed logs.
- Select an attribution source.
- Optionally configure inactivity timeout threshold in minutes.
- Configure your default domain and any advanced settings.
- Select syslog as your collection method and specify the port and protocol you identified during Cisco ACS configuration.
- Optionally choose to Encrypt the event source if choosing TCP by downloading the Rapid7 Certificate.
- Click the Save button.