Managing certificates for scanning
During scans, Nexpose checks Web sites and TLS or SSL servers for specific Root certificates to verify that these entities are validated by trusted Certificate Authorities (CAs).
The Security Console installation includes a number of preset certificates trusted by commonly used browsers from Microsoft, Google, Mozilla, and Apple. Additionally, you can import Root certificates that were expressly created by trusted CAs for targets that you want to scan.
The application reports a certificate signed by an unknown or untrusted entity as a vulnerability. A malicious party pretending to be a trusted entity can stage a man-in-the-middle attack, eavesdropping on TLS/SSL connections.
Importing custom certificates
The permission required for this task is Manage Global Settings, which typically belongs to a Global Administrator.
Make sure the custom certificate is a Root CA certificate. Otherwise, the full certificate chain cannot be validated during a scan. The certificate must be in Certificate Signing Request (CSR) / Privacy Enhanced Mail (PEM) base64 encoded format.
The .cer format is not supported.
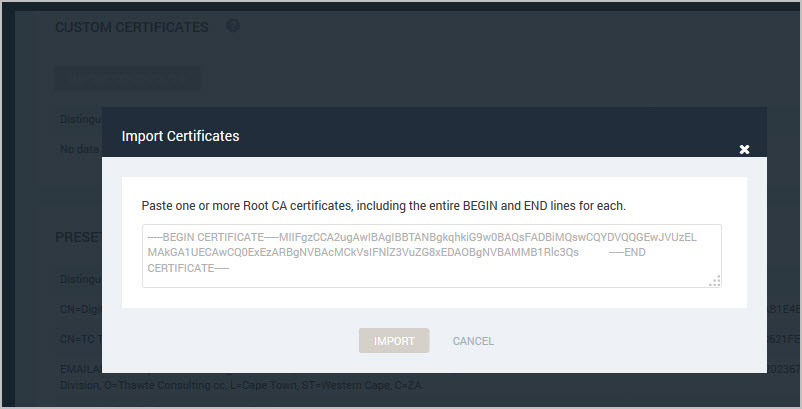
- Open the certificate file on the computer hosting it, and copy the contents of the file, including the entire BEGIN and END lines. Example:
-----BEGIN CERTIFICATE-----
MIIHQDCCBSigAwIBAgIJAMStF8UUH6doMA0GCSqGSIb3DQEBCwUAMIHBMQswCQYD
VQQGEwJVUzERMA8GA1UECBMITmVicmFza2ExFjAUBgNVBAcTDU5lYnJhc2thIENp
-----END CERTIFICATE------ Click the Administration icon in the Security Console Web interface.
- Click Scans > Root Certificates.
- On the Certificates page, click the Import Certificates button.
- Paste the copied certificate into the text box and click Import.
The certificate appears in the Custom Certificates table. You also can view preset certificates on the Root Certificates page.
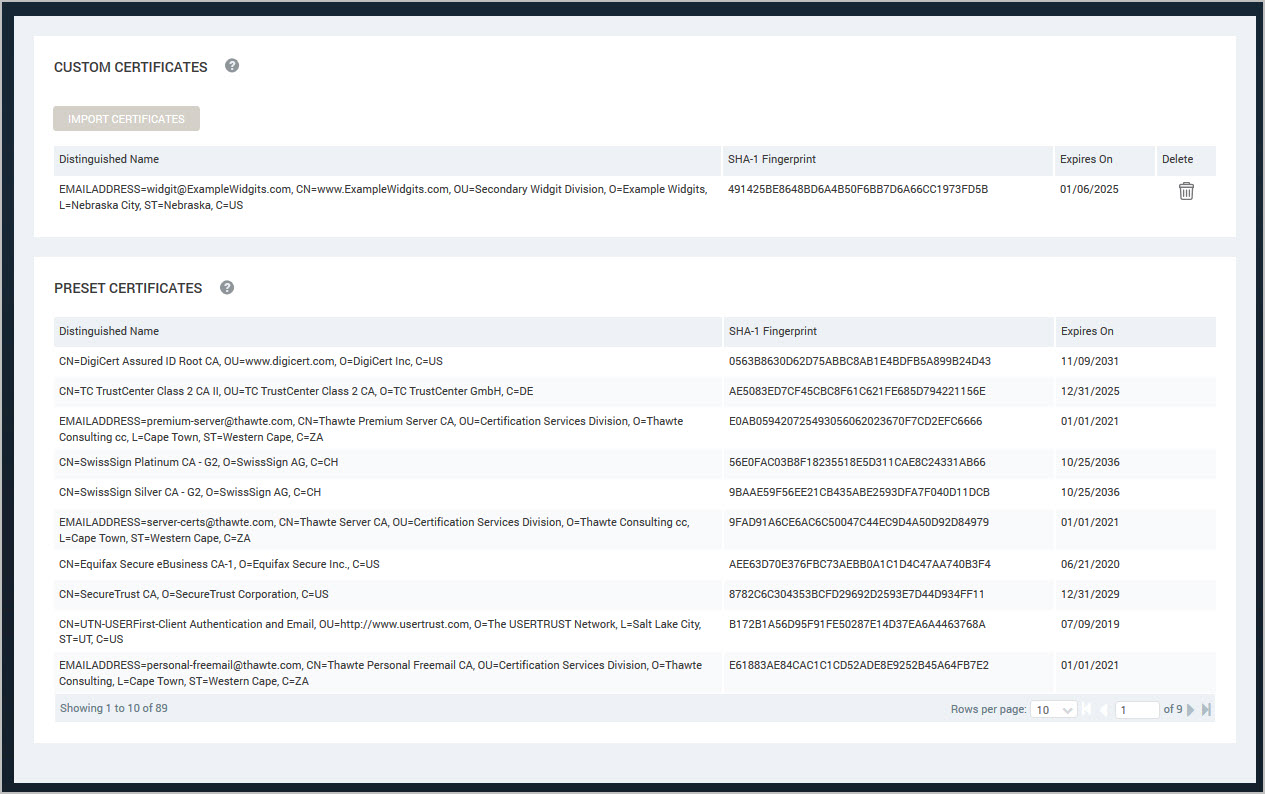
Removing certificates
Removing a root certificate from the trust store affects future scans in that any scanned certificates that were signed by the root certificate authority will no longer be trusted. They will be reported as vulnerabilities.
The permission required for removing custom certificates is Manage Global Settings, which typically belongs to a Global Administrator.
- Click the Administration icon in the Security Console Web interface.
- Click Scans > Root Certificates.
- On the Certificates page, find the certificate you want to delete from the Custom Certificates table.
- Click the Delete icon. The table refreshes and no longer displays the deleted certificate.
You cannot delete preset certificates.