Manage Meterpreter and Shell Sessions
After you successfully exploit a host, either a shell or Meterpreter session is opened. By default, Metasploit attempts to deliver a Meterpreter payload. A Meterpreter payload is uploaded to a remote machine that allows you to run Metasploit modules. If Metasploit is unable to deliver a Meterpreter payload then it opens a shell.
Depending on the module used to create a session, either a Shell or both a Shell and Meterpreter session will be opened. This is because shell payloads are created by running a command on a remote machine, and they can be easier to “launch”. Some exploits are limited in functionality ,and shell commands require less manipulation by the exploit.
A Meterpreter shell gives you access to Metasploit modules and other actions not available in the command shell.
A shell session opens a standard terminal on the target host, giving you similar functions to a terminal on your OS. The functionality can differ depending on the type of exploit used. Using a shell does not provide the same actions as a Meterpreter shell.
Command Shell
“Command Shell” is listed under Shell and Meterpreter. While the name is the same, the functionality is not. Meterpreter > Command Shell will open a Meterpreter shell, while Shell > Command Shell will open a standard terminal.
Manage Your Meterpreter Session
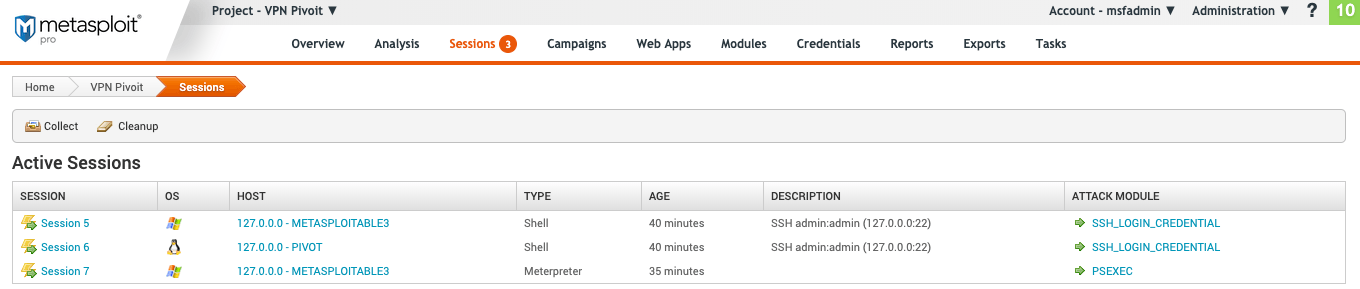
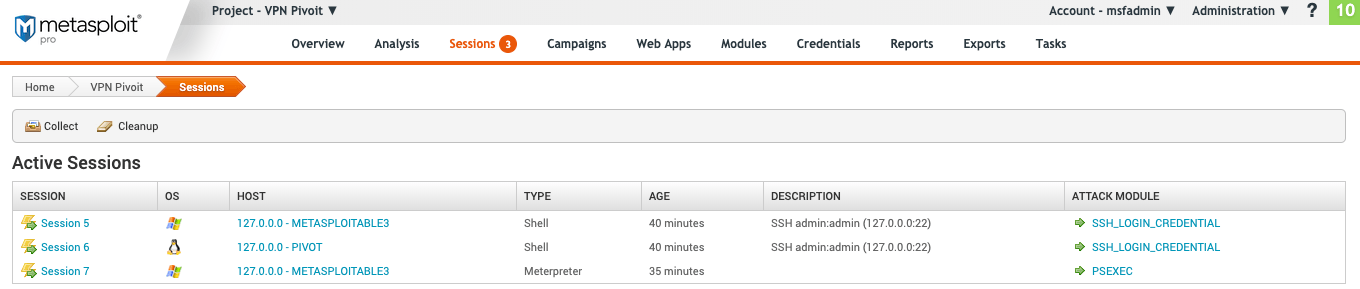
To access the session pages in the top menu go to “Sessions”.
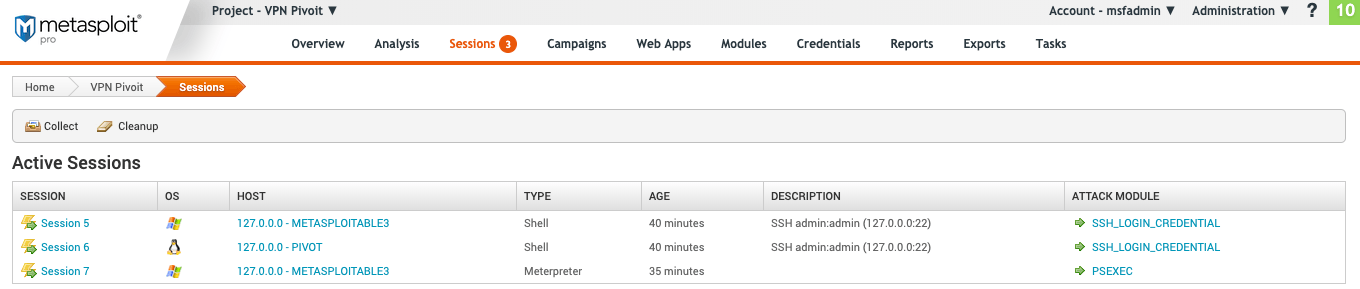
The Meterpreter “Active Sessions” page provides you with the following information:
- Session - The number of the session. These are attached to the session in sequential order of being created.
- OS - The host operating system.
- Host - The host address and name.
- Type - The type of shell.
- Age - The time the session has been opened in minutes or seconds. Once 60 seconds is reached, time is tracked in minutes.
- Description - Any information related to how the session was opened if available. For example, bruteforce opened sessions will contain the username and password used.
- Attack Module - The exploit used to open the session.
View Available Meterpreter Actions
To see all the available actions for a Meterpreter shell during a session, do the following:
- Under “Active Sessions” select a session that has a “Type” of “Meterpreter”.
- On the session page, review the available actions. From this page, you can launch a terminal, see available modules and run post-exploitation actions.
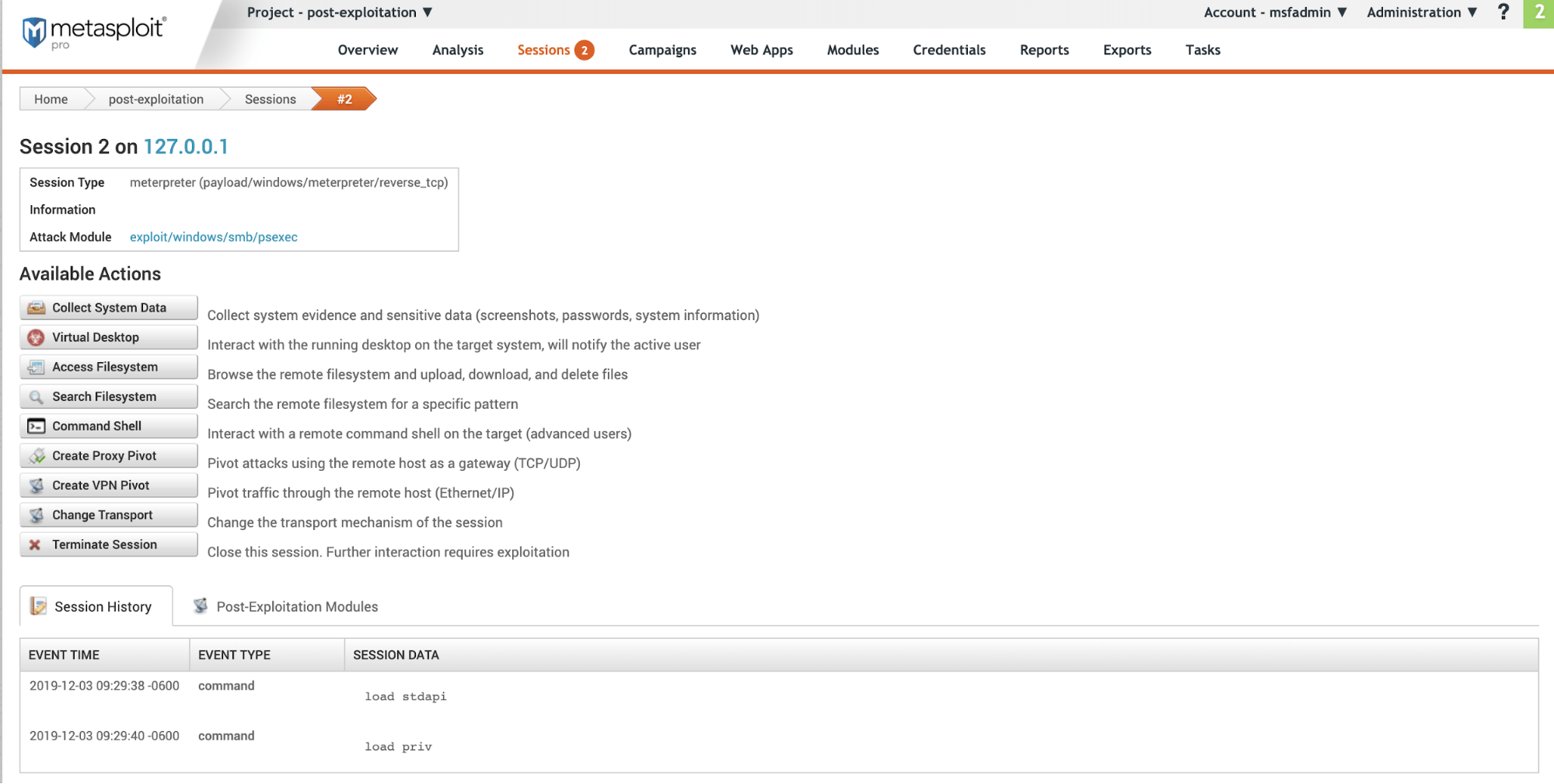
The Meterpreter session page has the following information:
- Session - Session number and target host address. In the image above this is
Session 2 on 127.0.0.1 - Session Type - The type of payload and module used to open the session.
- Information - Any information on how the session was opened. If this was the result of a bruteforce attack it will include the authentication type and credential pair used.
- Attack Module - Exploit used to open the session.
- Available Actions - All the available actions that can be taken.
- Session History - A detailed list of all actions taken during an open session.
- Post-Exploitation Modules - Modules available to run based on the OS and payload type.
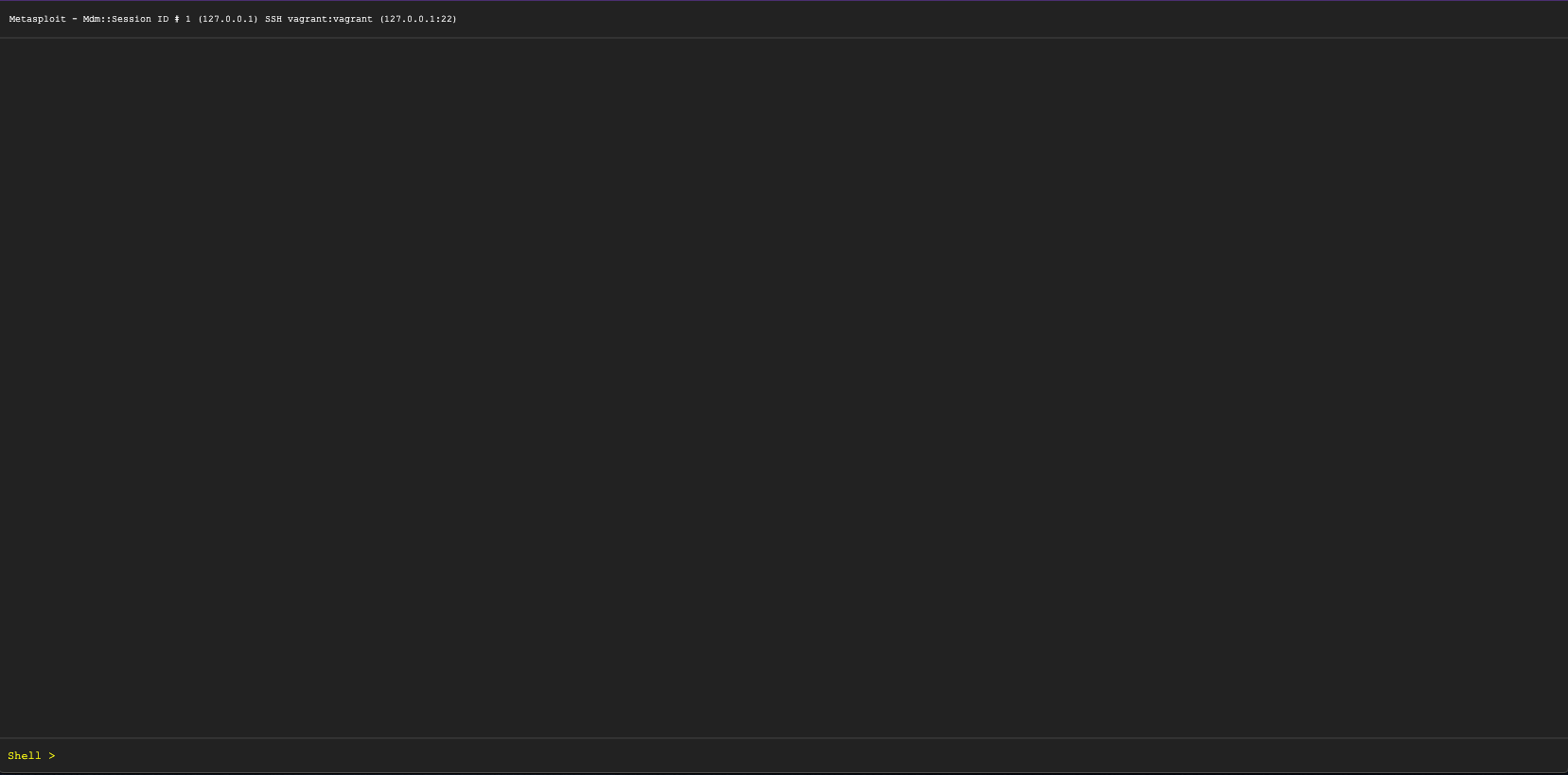
Launch the Meterpreter Command Shell
Under “Available Actions” click Command Shell. It will open a blank terminal.
At the top is the session ID and the target host address. In this example, the session ID is :
Metasploit - Mdm::Session ID # 2 (127.0.0.1)
At the bottom is the shell input. Meterpreter >
View Available Meterpreter Shell Commands
-
To see a list of available commands type
?.Meterpreter > ?It will display a list of available commands with a description of each. From here you can run a module, review the target hosts files and get networking information. -
To shut down a session from the shell use
quit.
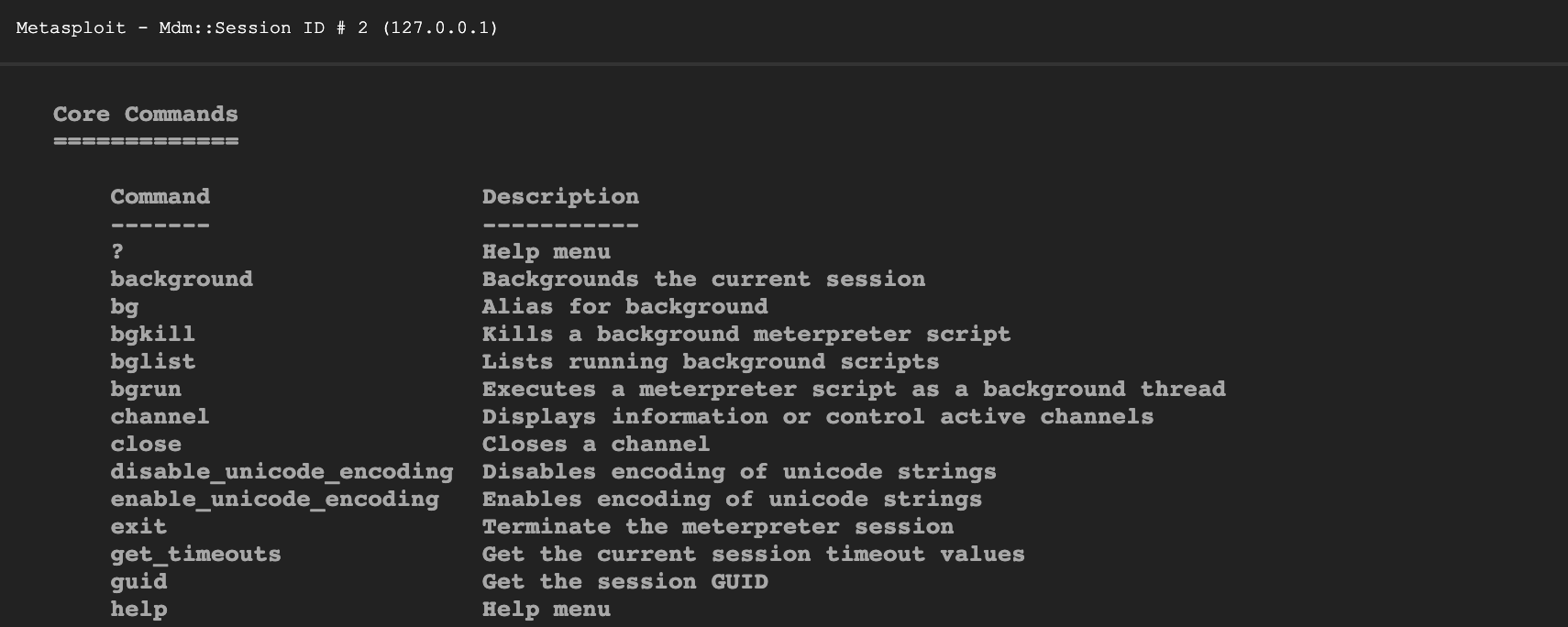
Meterpreter Shell Commands
Core Commands
=============
Command Description
------- -----------
? Help menu
background Backgrounds the current session
bg Alias for background
bgkill Kills a background meterpreter script
bglist Lists running background scripts
bgrun Executes a meterpreter script as a background thread
channel Displays information or control active channels
close Closes a channel
disable_unicode_encoding Disables encoding of unicode strings
enable_unicode_encoding Enables encoding of unicode strings
exit Terminate the meterpreter session
get_timeouts Get the current session timeout values
guid Get the session GUID
help Help menu
info Displays information about a Post module
irb Open an interactive Ruby shell on the current session
load Load one or more meterpreter extensions
machine_id Get the MSF ID of the machine attached to the session
migrate Migrate the server to another process
pivot Manage pivot listeners
pry Open the Pry debugger on the current session
quit Terminate the meterpreter session
read Reads data from a channel
resource Run the commands stored in a file
run Executes a meterpreter script or Post module
secure (Re)Negotiate TLV packet encryption on the session
sessions Quickly switch to another session
set_timeouts Set the current session timeout values
sleep Force Meterpreter to go quiet, then re-establish session.
transport Change the current transport mechanism
use Deprecated alias for "load"
uuid Get the UUID for the current session
write Writes data to a channel
Stdapi: File system Commands
============================
Command Description
------- -----------
cat Read the contents of a file to the screen
cd Change directory
checksum Retrieve the checksum of a file
cp Copy source to destination
dir List files (alias for ls)
download Download a file or directory
edit Edit a file
getlwd Print local working directory
getwd Print working directory
lcd Change local working directory
lls List local files
lpwd Print local working directory
ls List files
mkdir Make directory
mv Move source to destination
pwd Print working directory
rm Delete the specified file
rmdir Remove directory
search Search for files
show_mount List all mount points/logical drives
upload Upload a file or directory
Stdapi: Networking Commands
===========================
Command Description
------- -----------
arp Display the host ARP cache
getproxy Display the current proxy configuration
ifconfig Display interfaces
ipconfig Display interfaces
netstat Display the network connections
portfwd Forward a local port to a remote service
resolve Resolve a set of host names on the target
route View and modify the routing table
Stdapi: System Commands
=======================
Command Description
------- -----------
clearev Clear the event log
drop_token Relinquishes any active impersonation token.
execute Execute a command
getenv Get one or more environment variable values
getpid Get the current process identifier
getprivs Attempt to enable all privileges available to the current process
getsid Get the SID of the user that the server is running as
getuid Get the user that the server is running as
kill Terminate a process
localtime Displays the target system's local date and time
pgrep Filter processes by name
pkill Terminate processes by name
ps List running processes
reboot Reboots the remote computer
reg Modify and interact with the remote registry
rev2self Calls RevertToSelf() on the remote machine
shell Drop into a system command shell
shutdown Shuts down the remote computer
steal_token Attempts to steal an impersonation token from the target process
suspend Suspends or resumes a list of processes
sysinfo Gets information about the remote system, such as OS
Stdapi: User interface Commands
===============================
Command Description
------- -----------
enumdesktops List all accessible desktops and window stations
getdesktop Get the current meterpreter desktop
idletime Returns the number of seconds the remote user has been idle
keyboard_send Send keystrokes
keyevent Send key events
keyscan_dump Dump the keystroke buffer
keyscan_start Start capturing keystrokes
keyscan_stop Stop capturing keystrokes
mouse Send mouse events
screenshare Watch the remote user's desktop in real time
screenshot Grab a screenshot of the interactive desktop
setdesktop Change the meterpreters current desktop
uictl Control some of the user interface components
Stdapi: Webcam Commands
=======================
Command Description
------- -----------
record_mic Record audio from the default microphone for X seconds
webcam_chat Start a video chat
webcam_list List webcams
webcam_snap Take a snapshot from the specified webcam
webcam_stream Play a video stream from the specified webcam
Stdapi: Audio Output Commands
=============================
Command Description
------- -----------
play play an audio file on target system, nothing written on disk
Priv: Elevate Commands
======================
Command Description
------- -----------
getsystem Attempt to elevate your privilege to that of local system.
Priv: Password database Commands
================================
Command Description
------- -----------
hashdump Dumps the contents of the SAM database
Priv: Timestomp Commands
========================
Command Description
------- -----------
timestomp Manipulate file MACE attributesManage your Shell Session
The Shell session page provides you with the following information:
- **Session - **Session number and target host address. In the image above this is
Session 2 on 127.0.0.1 - **Session Type - **The type of payload and module used to open the session.
- Information - Any information on how the session was opened. If this was the result of a bruteforce attack it will include the authentication type and credential pair used.
- Attack Module - Exploit used to open the session.
- **Available Actions - **All the available actions that can be taken.
- **Session History - **A detailed list of all actions taken during an open session.
- **Post-Exploitation Modules - **Modules available to run based on the OS and payload type.
View Available Shell Actions
- Under “Active Session” select a session that has a “Type” of “Shell”.
- Review the shell session page. From this page, you can launch a shell and run post-exploitation actions. Since this is a shell session, the available “Post-Exploitation Modules” will not be the same as a Meterpreter session. They will depend on the exploit used.
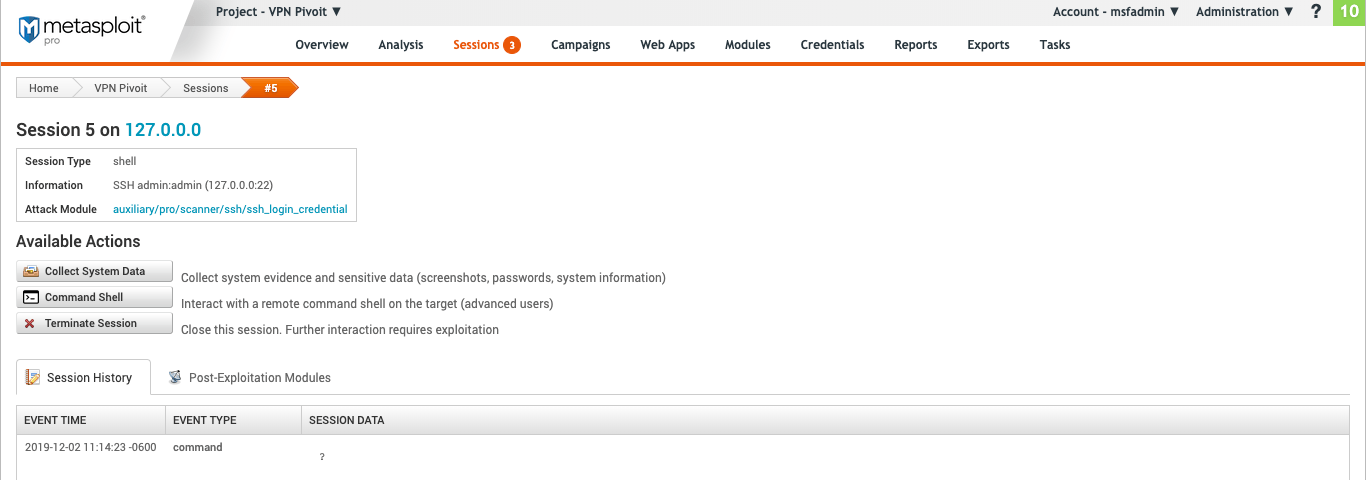
The Shell session page has the following information:
- **Session - **Session number and target host address. In the image above this is
Session 2 on 127.0.0.1 - **Session Type - **The type of payload and module used to open the session.
- Information - Any information on how the session was opened. If this was the result of a bruteforce attack it will include the authentication type and credential pair used.
- Attack Module - Exploit used to open the session.
- **Available Actions - **All the available actions that can be taken.
- **Session History - **A detailed list of all actions taken during an open session.
- **Post-Exploitation Modules - **Modules available to run based on the OS and payload type.
Launch a Command Shell
Under “Available Actions” click Command Shell. It will then open a blank terminal.
The session ID and the target host address are displayed at the top of the command shell. In this example, the session ID is : Metasploit - Mdm::Session ID # 1 (127.0.0.1) SSH vagrant:vagrant (127.0.0.1:22)
At the bottom is the shell input. Shell >
The commands available for the shell will depend on the target host OS.