Integrate a Carbon Black Response Cloud Device
Configure a Carbon Black Response cloud device to receive IOCs from Digital Risk Protection (Threat Command). When you add the device to Digital Risk Protection (Threat Command), it will be configured to receive IOCs.
Add a Carbon Black Response cloud device to Digital Risk Protection (Threat Command)
Add a cloud device to Digital Risk Protection (Threat Command).
Prerequisites
- You have the credentials to access the device.
- You have administrative credentials to access Digital Risk Protection (Threat Command) with a subscription to the Automation and TIP modules.
To add a cloud device to Digital Risk Protection (Threat Command):
- Log in to Digital Risk Protection (Threat Command) at https://dashboard.ti.insight.rapid7.com
- From the main menu, select Automation -> Integrations.
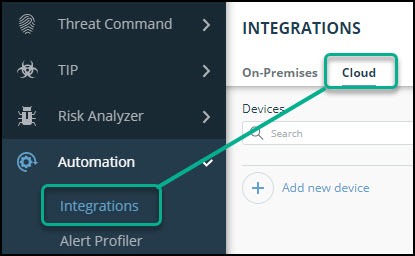
- From the Integrations page, click Cloud.
- Click Add new device.
- In the Add New Cloud Device dialog, type a user-defined name for the device. The name can contain a maximum of 50 letters, spaces, numbers, and underscores.
- Select the Device type.
The default device IOCs limit is displayed. - (Optional) You can change the IOCs limit.
- Click Add.
- To verify that the new device is added, refresh the Automation > Integrations page.
The new device is added to the cloud integrations device list. Next to the device name, there is a red dot, indicating that communication has not yet been established. The dot will change to green when the device is synchronized. If the device cannot synchronize for more than 48 hours, an email warning is sent to the account administrator.
Configure a Carbon Black Response cloud device to pull IOCs
After a device has been added, you must enable the pulling of IOCs by the Carbon Black Response device from Digital Risk Protection (Threat Command).
Before you begin, ensure:
- You have the device login credentials.
- The device has been added.
- You have administrative credentials to access Digital Risk Protection (Threat Command) with a subscription to the Automation and TIP modules.
- An IOC group for this device exists in Digital Risk Protection (Threat Command).
Creating IOC groups is described in Create an IOC group
Digital Risk Protection (Threat Command) supports IOC groups of domains, IP addresses, and MD5 file hashes only.
To configure a Carbon Black Response cloud device:
-
Log in to the Carbon Black management console.
-
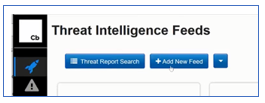
Navigate to Threat Intelligence.
-
Click Add New Feed.
-
From Digital Risk Protection (Threat Command), copy the Carbon Black device URL and authentication details into Carbon Black:
- From Digital Risk Protection (Threat Command), select Automation > Integrations.
- From the Cloud device list, select the Carbon Black Response device.
- From the top of the page, click Device Details.
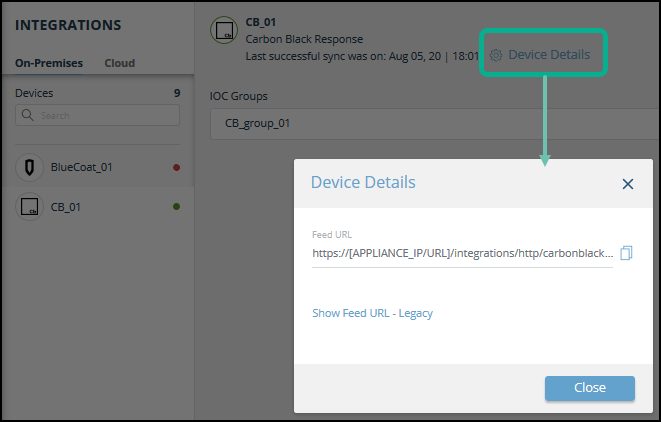
- Paste the full Feed URL from Digital Risk Protection (Threat Command) into the Carbon Black Edit Alliance Feed dialog:
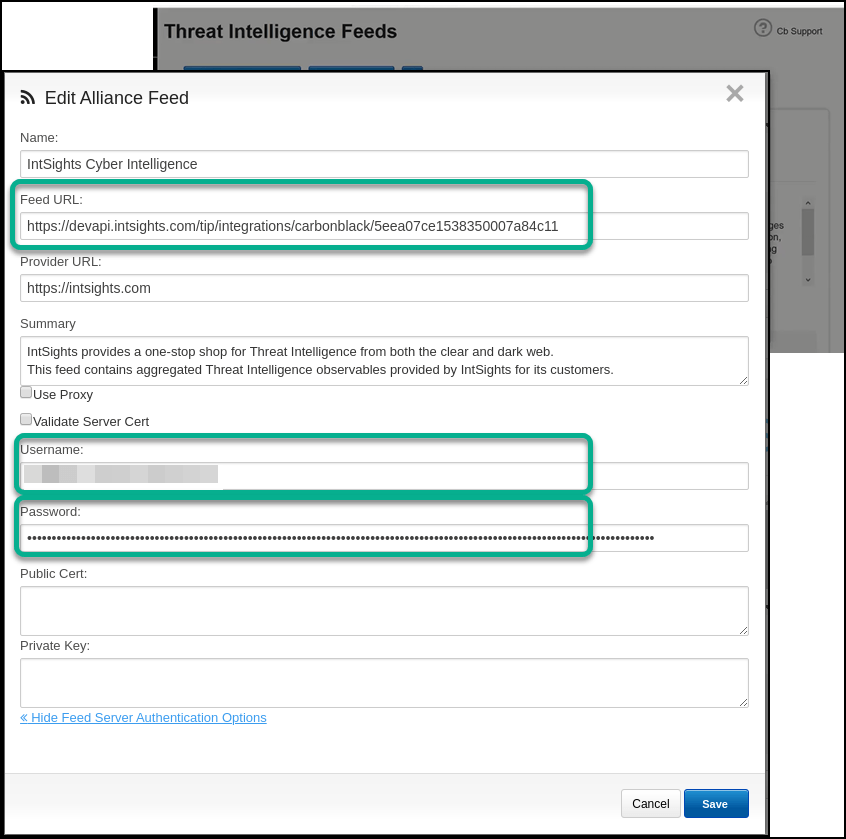
- From the Digital Risk Protection (Threat Command) Settings > Subscriptionpage, copy and paste these values:
- Copy the Digital Risk Protection (Threat Command) Account ID to the Carbon Black Username.
- Copy the Digital Risk Protection (Threat Command) API key to the Carbon Black Password.
For more information about generating, revoking, and displaying these credentials, see API key, account ID, and appliance key.
- Click Save.
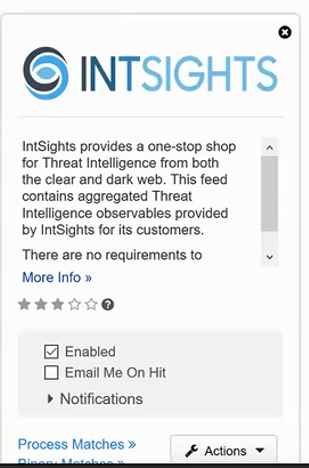
- In the feed, select Enabled.
-
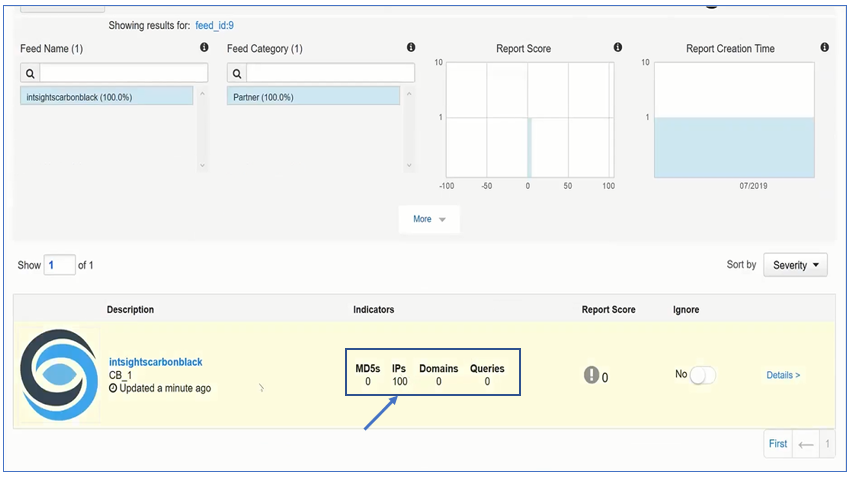
In the Carbon Black management console, verify that IOCs are being received: