InsightIDR Overview
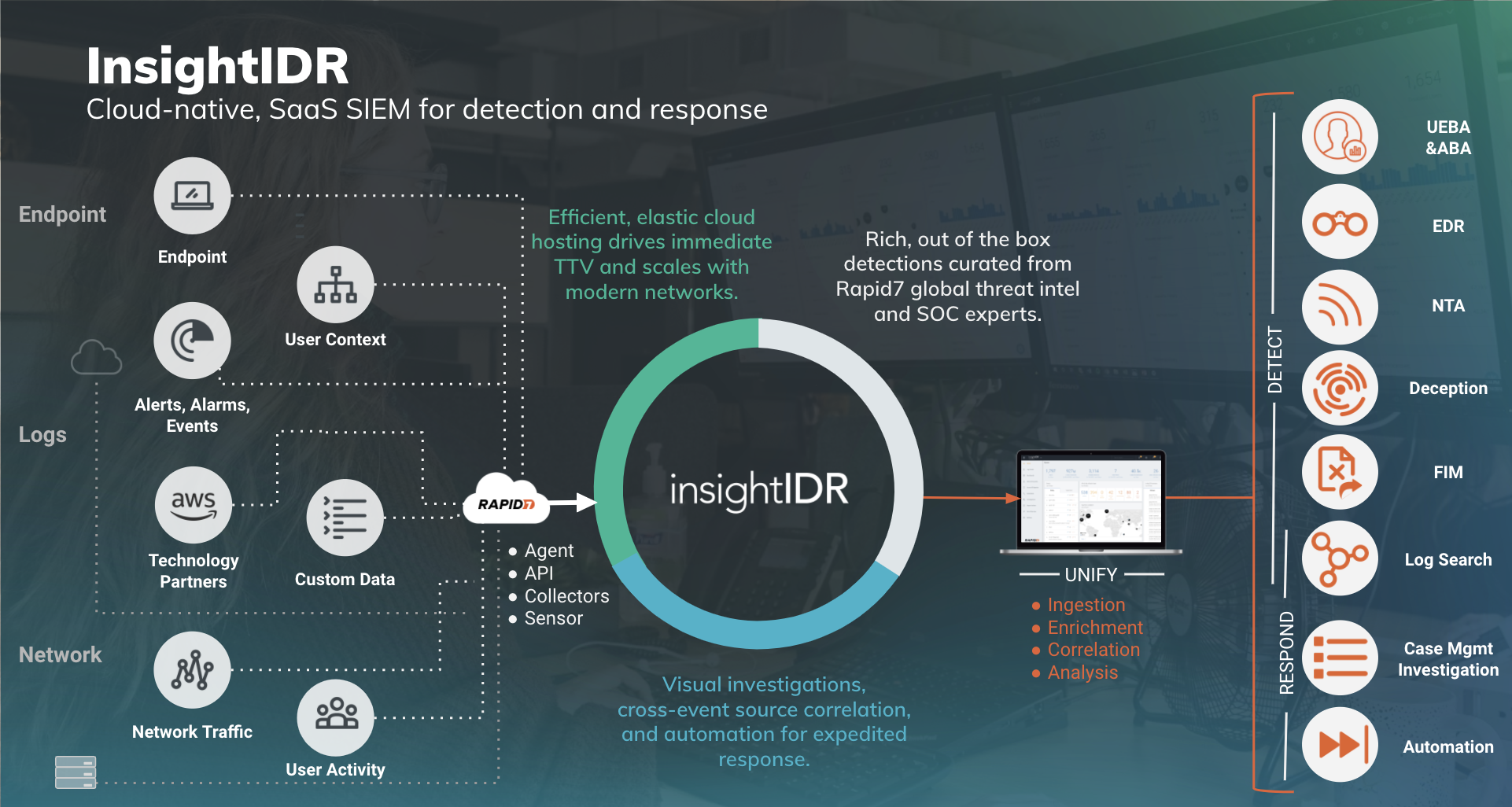
Rapid7’s InsightIDR is your security center for incident detection and response, authentication monitoring, and endpoint visibility. Together, these form Extended Detection and Response (XDR). InsightIDR identifies unauthorized access from external and internal threats and highlights suspicious activity so you don’t have to weed through thousands of data streams. XDR accelerates more comprehensive threat detection and response. This cloud-native, cloud-scalable security solution can unify and transform multiple telemetry sources. Read more about XDR in Rapid7's blog.
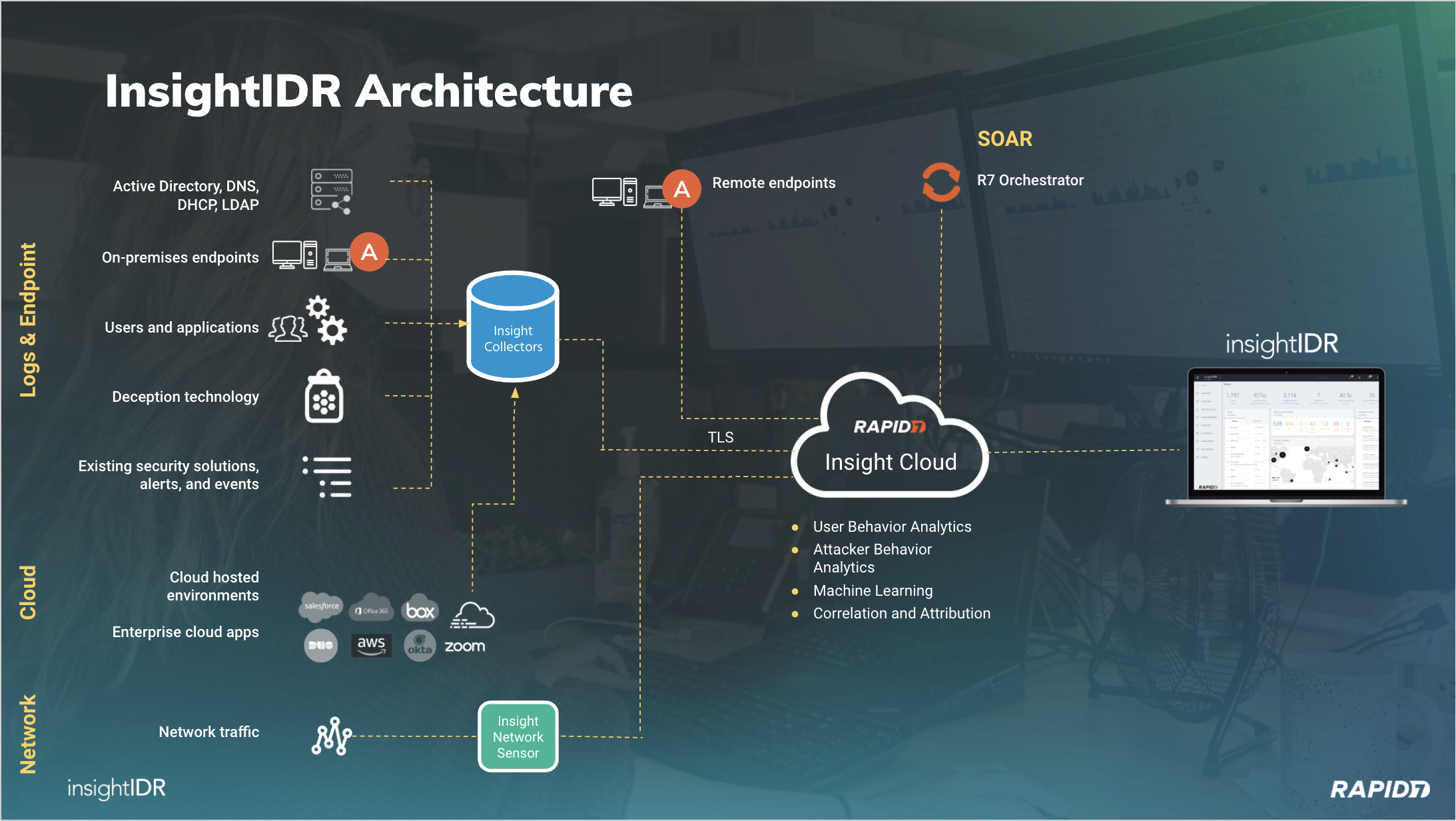
InsightIDR combines the full power of endpoint forensics, log search, and sophisticated dashboards into a single solution. It is a Software as a Service (SaaS) tool that collects data from your existing network security tools, authentication logs, and endpoint devices. InsightIDR then aggregates the data at an on-premises Collector or a dedicated host machine that centralizes your data.
Use this Collector to gather and transmit your logs securely to Amazon Web Services (AWS), which hosts customer databases and the web interface. Rapid7 runs analytics on this data to correlate users, accounts, authentications, alerts, and privileges. The analysis provides insight into user behavior while searching for known indicators of compromise.
Rapid7 recommends keeping dedicated Collectors on-premises to collect event data, log data, and endpoint data.
For real-time endpoint data collection, install the Insight Agent on your assets.
Getting Started with InsightIDR
We offer three different InsightIDR packages for you to choose from based on your security needs: InsightIDR Essential, InsightIDR Advanced, and InsightIDR Ultimate.
We've created individualized Quick Start Guides to help you get started with InsightIDR. Navigate to the version that aligns with your product!
- InsightIDR Essential | Quick Start Guide: Your basic security incident and event management tool to meet your compliance requirements.
- InsightIDR Advanced | Quick Start Guide: Your core security incident and event management tool for detection and response.
- InsightIDR Ultimate | Quick Start Guide: Your security incident and event management tool for extended detection and response (XDR).
Unsure about which Quick Start Guide is for you?
If you purchased InsightIDR (not designated as Essential, Advanced, or Ultimate), please follow InsightIDR Quick Start Guide | Advanced for tasks and materials suited to your product.
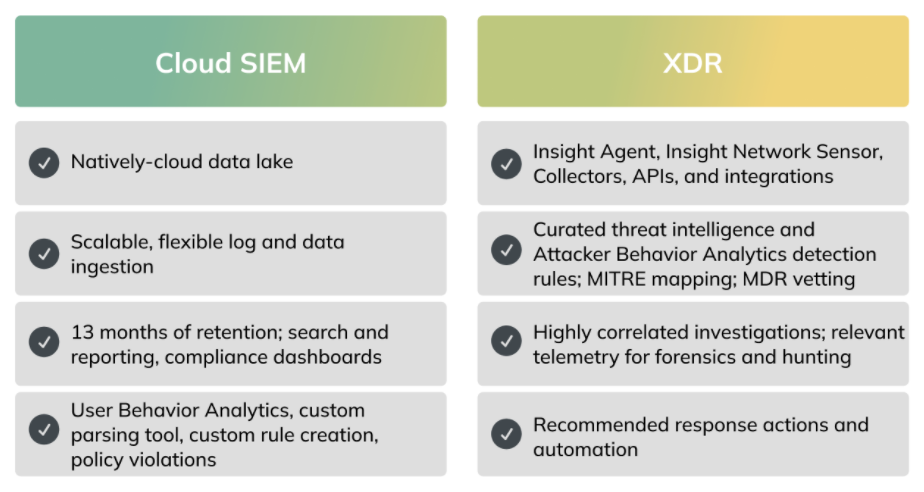
InsightIDR is your CloudSIEM for Extended Detection and Response
InsightIDR—Rapid7’s natively cloud Security Information and Event Monitoring (SIEM) and Extended Detection and Response (XDR) solution—delivers accelerated detection and response through:
- A frictionless deployment experience
- Intuitive SaaS interface
- Comprehensive environment visibility
- Expertly vetted detections
- Embedded threat intelligence
- Powerful investigation tools
- Automated response capabilities
XDR unifies and transforms relevant security data from across your modern environment to detect real attacks and provide security teams with high-context, actionable insights to investigate and extinguish threats faster.
InsightIDR helps customers achieve SIEM and XDR outcomes
Why Use InsightIDR?
When you connect all of the various data streams to InsightIDR, you can take advantage of all the following built-in features made with users in mind:
- Unify Your Data Into a Single Security View: Track user network resources, their devices, and their visited cloud services. InsightIDR normalizes network data and attributes it to users, so you know the origin, owner, and time of event.
- Analyze Raw Logs, Endpoint Data, and Network Traffic: InsightIDR collects data streams from every possible place and brings them together in one convenient place for you to analyze. Sift through raw logs, visualize your endpoint data, or organize your network traffic from users.
- Receive Alerts for Suspicious Activity: Whether or not suspicious activity is happening on your network, InsightIDR sets up traps that alert you of security gaps.
- Prioritize Events: Because traffic and data is normalized, InsightIDR automatically prioritizes network events and brings notable events to your attention. InsightIDR filters out non-critical events so you can focus on the important ones.
- Investigate Events: In the event of a breach, security teams will have contextual information of compromised data, time of event, and possible next actions of the intruder.
- Monitor Your Security Operations Activities: The Security Operations Activity dashboard synthesizes your data into actionable insights, making it easier to respond to alerts, report on threat trends, and analyze the overall effectiveness of your security team.
InsightIDR in Action
Various Operation departments use InsightIDR at companies large and small, but an Information Security (InfoSec) team, uses InsightIDR everyday to keep a network safe. To keep their network safe, the InfoSec team might:
- Investigate an alert and confirm suspicious behavior on the Investigations page.
- Look over details and activity collected in an incident, such as time, users, activity, and assets involved.
- Gather evidence and monitor users and assets by using the Watchlist or Restricted Asset list.
- Contextualize suspicious behavior by searching logs, browsing through firewall activity, or combing through IP addresses.
Incident Response
While many incidents can be false alarms, InsightIDR contextualizes malicious events so that an InfoSec team can properly respond. If they need to, InfoSec can wipe an asset, reinstall a clean OS, and start over. In extreme cases, InfoSec can destroy an asset that is beyond repair.