Varonis DatAdvantage
Varonis DatAdvantage gives you visibility and control over your data and hybrid IT infrastructure by mapping who accesses your data across file and email systems. If you’re a Varonis DatAdvantage customer, you can set up an integration to forward DatAdvantage alerts to SIEM (InsightIDR). This third-party alerts integration saves you time spent reviewing alerts in 2 places, and allows you to leverage investigation features in IDR for DatAdvantage events.
To set up the Varonis DatAdvantage integration, you’ll need to:
- Set up the Varonis DatAdvantage Event Source in SIEM (InsightIDR)
- Configure Varonis DatAdvantage Alert Forwarding
Configure SIEM (InsightIDR) to collect data from the event source
After you complete the prerequisite steps and configure the event source to send data, you must add the event source in SIEM (InsightIDR).
To configure the new event source in SIEM (InsightIDR):
- From the left menu, go to Data Collection and click Setup Event Source > Add Event Source.
- Do one of the following:
- Search for Varonis DatAdvantage in the event sources search bar.
- In the Product Type filter, select Third Party Alerts.
- Select the Varonis DatAdvantage event source tile.
- Choose your collector and event source. You can also name your event source if you want.
- If you are sending additional events beyond alerts, select the unparsed logs option.
- Specify an unused port on the collector that can receive forwarded Varonis alerts. We recommend you use TCP as your protocol.
Port Number and IP Address
Note the port number as well as the IP address associated with your IDR collector. You will need both to configure your Varonis syslog server address later.
- Click Save.
Configure Varonis DatAdvantage Alert Forwarding
After configuring the Varonis DatAdvantage event source in SIEM (InsightIDR), you can configure DatAdvantage to forward alerts to IDR. There are 3 tasks in this configuration procedure:
- Task 1: Configure the syslog server address in Varonis DatAdvantage
- Task 2: Create a CEF or LEEF syslog message forwarding template
- Task 3: Set up alerts for single or multiple rules
Task 1: Configure the syslog server address in Varonis DatAdvantage
- Log in to Varonis DatAdvantage.
- Select Tools > DatAlert.
- From the left menu, select Configuration.
- Specify values for these fields in the “Syslog Message Forwarding” section:
- Syslog server IP address: SIEM (InsightIDR) collector IP address
- Port: Port number associated with the event source you set up in Insight IDR
Task 2: Create a CEF or LEEF syslog message forwarding template
- From the left menu in DatAlert, select Alert Templates.
- Click the green plus sign. The “Add Alert Template” dialog box appears.
- Enter a Template name.
- From the “Apply to alert methods” dropdown menu, select Syslog message.
- Create a new Alert Template Format using the example templates below.
Use this example to send alerts in CEF format.
CEF:0|Varonis|DatAdvantage|<DatAdvantage version>|<Event Op Code>|<Event Type>|<Severity>|rt=<Alert Time> cat=Alert cs2=<Rule Name> cs2Label=RuleName cn1=<Rule ID> cn1Label=RuleID end=<Event Time> duser=<Acting Object> dhost=<File Server/Domain> filePath=<Access Path> fname=<Affected Object> act=<Event Type> dvchost=<Device Name> dvc=<Device IP Address> outcome=<Event Status> msg=<Additional Data> cs3=<Attachment Name> cs3Label=AttachmentName cs4=http://<DLS_IP_ADDRESS>/DatAdvantage/#/app/analytics/entity/Alert/<Alert ID> cs4Label=AlertURL deviceCustomDate1=<Mail Date> fileType=<Mail Item Type> cs1=<Mail Recipients> cs1Label=MailRecipient suser=<Mail Source> cs5=<Mailbox Access Type> cs5Label=MailboxAccessType cnt=<Threshold> cs6=<Changed Permissions> cs6Label=ChangedPermissions oldFilePermission=<Permissions Before Change> filePermission=<Permissions After Change> dpriv=<Trustee> start=<First Event Time> externalId=<Alert ID>Use this example to send alerts in LEEF format.
LEEF:9.1.0|Varonis|DatAdvantage|<DatAdvantage Version>|<file| cat=<Alert Category> devTime=<Alert time> devTimeFormat=MMM dd yyyy HH:mm:ss proto=Syslog sev=<Severity> src=<Device IP Address> Device_Name=<Device Name> Alert_Description=<Alert Description> usrName=<Acting Object> accountName=<Acting Object SAM Account Name> domain=<Acting Object Domain Name> Event_Type=<Event Type> Event_Type_ID=<Event Op Code> Event_Status=<Event Status> Affected_Object=<Affected Object> Event_File_Server_Domain=<File Server/Domain> Affected_Object_Path=<Path> Event_Additional_Data=<Additional data> Threshold_Value=<Threshold> Threshold_First_Timestamp=<First event time> Event_by_MailboxOwner=<Client Access Type> Email_Sender=<Mail Source> Email_Date=<Mail Date> Account_of_Changed_Permissions=<Trustee> Permissions_Changes=<Changed Permissions> Permissions_before_Change=<Permissions Before Change> Permissions_after_Change=<Permissions After Change> Alert_Page_URL=<Alert page URL> Alert_ID=<Alert ID>- Click OK, and verify that the new template appears in the “Alert Templates” table.
- Click OK.
Task 3: Set up alerts for single or multiple rules
You set up rules in Varonis DatAdvantage regarding which behaviors cause alerts. To complete your integration, you have to associate those rules with the syslog connection you configured in Task 1 by selecting the Syslog alert method for each rule.
To select the Syslog alert method for a single rule:
- From the DatAlert rules table, select the rule, then click Edit Rule. The rule editing menu appears.
- From the left menu, select Alerts Method. The “Alert Method” window appears.
- Select Syslog message.
- Select UDP as the Protocol.
- Click OK.
To select the Syslog alert method for multiple rules:
- From the DatAlert rules table, select the rules, then click Edit Rule. The rule editing menu appears.
- From the left menu, select Alerts Method. The “Alert Method” window appears and its contents are disabled for selection.
- Click the edit icon for the Syslog message option, then click the checkbox next to Syslog message.
- Click OK.
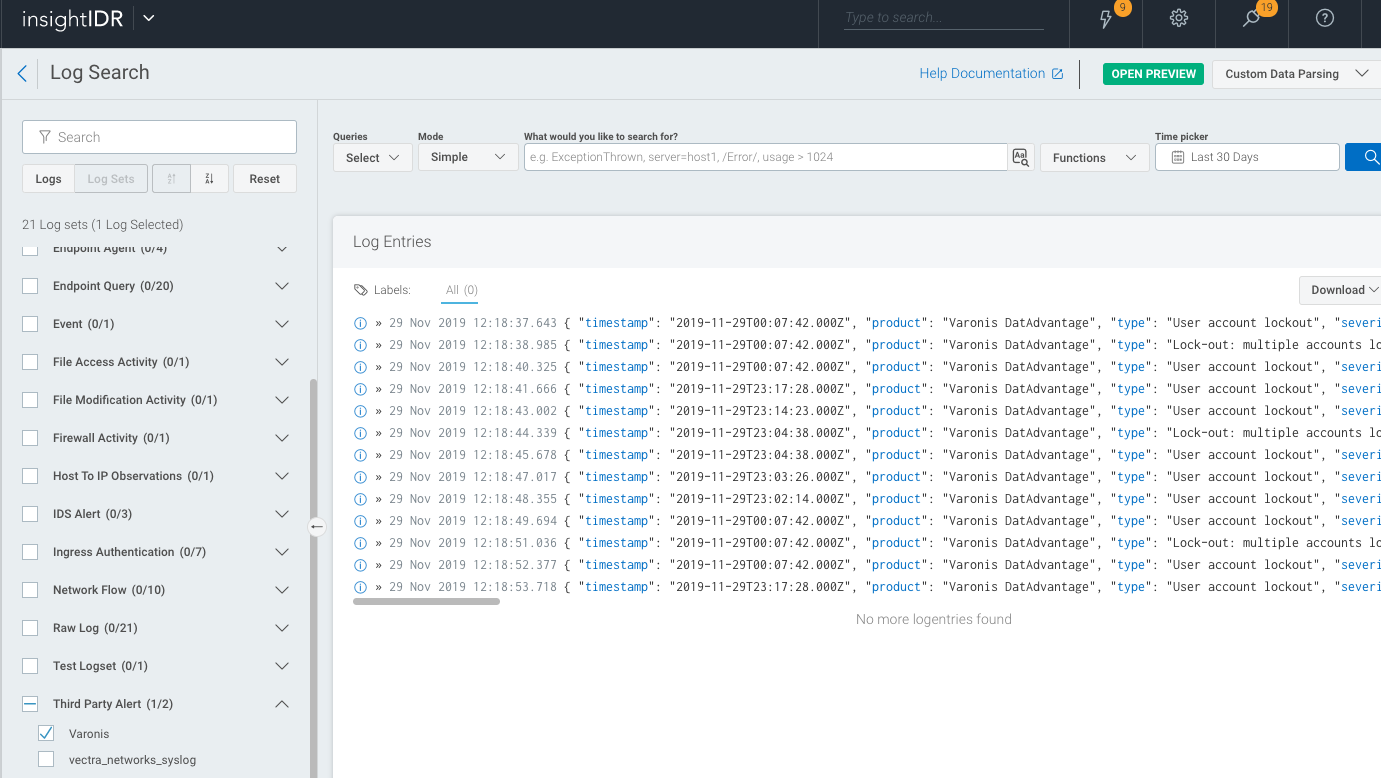
Verify the Configuration
After configuring the Varonis DatAdvantage event source and alert forwarding, you can perform a log search for Varonis alerts in SIEM (InsightIDR) to verify they are forwarding successfully.
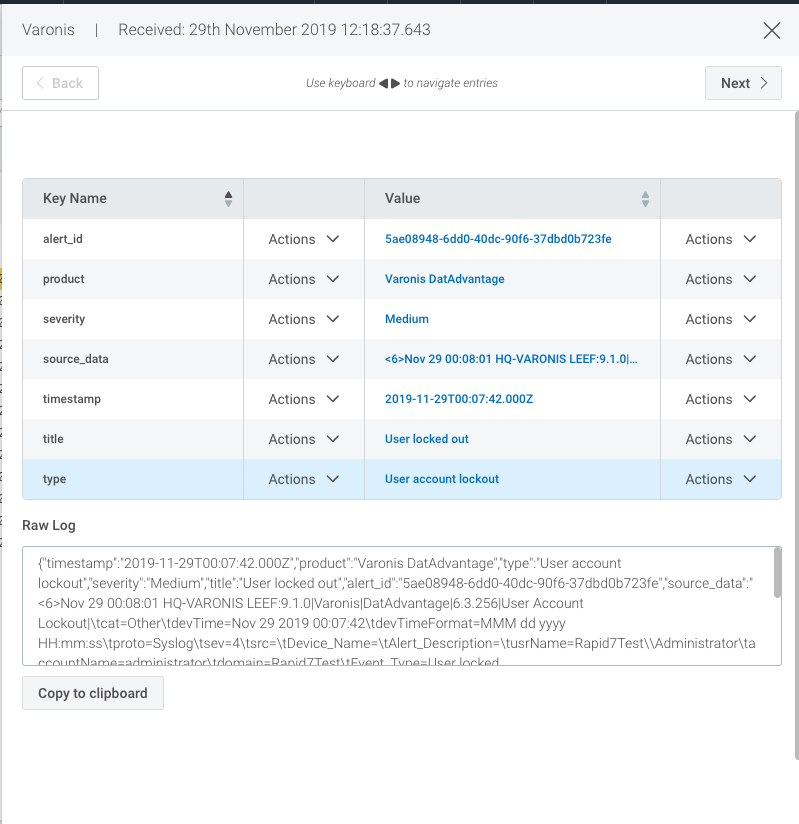
When DatAdvantage alerts appear in SIEM (InsightIDR), you’ll notice their associated severity rankings are converted to match SIEM (InsightIDR) conventions. Here’s what each alert severity means in SIEM (InsightIDR).
- Red - High severity
These alerts have a DatAdvantage severity of Emergency, Alert, or Critical. - Orange - Medium severity
These alerts have a DatAdvantage severity of Error or Warning. - Green - Low severity
These alerts have a DatAdvantage severity of Notice, Informational, or Debug.